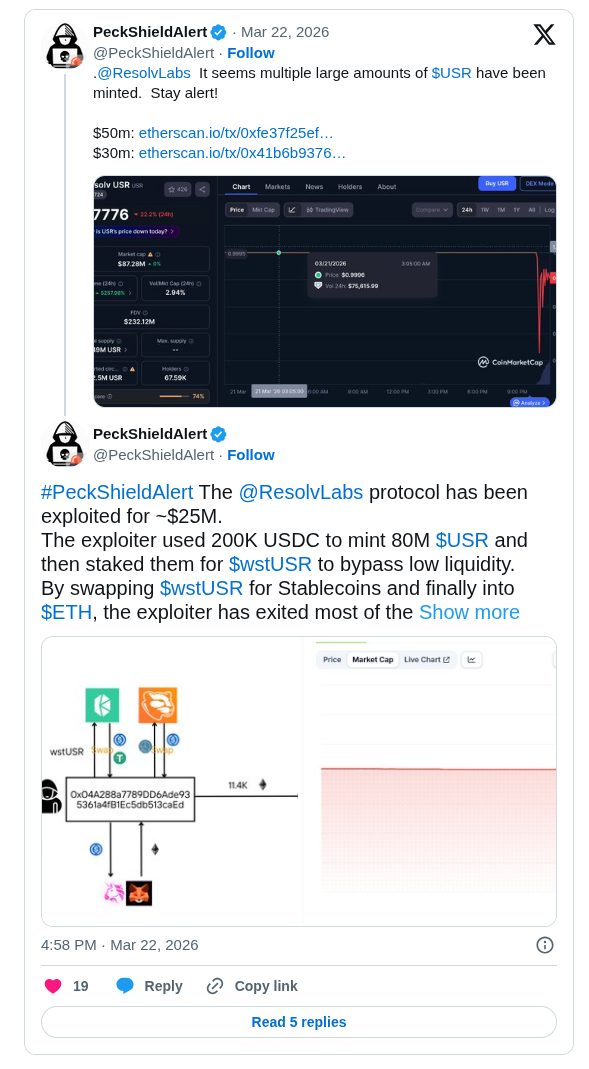
PeckShieldAlert identified a major security breach at Resolv Labs on March 22 in which an attacker extracted approximately 25 million dollars by minting unbacked USR tokens on Ethereum. The exploiter deposited a modest 200,000 USDC to generate a staggering 80 million USR by leveraging vulnerabilities in the protocol minting logic. To evade immediate liquidity limits and minimize price slippage the attacker staked the minted supply into wstUSR and subsequently converted the holdings through stablecoin pairs like USDC and USDT on platforms such as Curve. The final proceeds were converted into native ETH before the protocol could intervene causing the USR price to violently depeg and crash by 80 percent.
Attack Execution and Technical Flaws
The breach originated from inadequate on chain validation within the USR minting and swap mechanics. Analysts believe the flaw stemmed from gaps in the targetAmount parameter validation in the requestSwap and completeSwap functions possibly combined with a compromised SERVICE ROLE signer that permitted unauthorized oversized outputs. PeckShieldAlert flagged two prominent transactions involving roughly 50 million tokens and another for 30 million which triggered immediate alerts. This intermediate conversion to wstUSR enabled seamless downstream trades allowing for a rapid and efficient drain of value within minutes of the initial activation.
Depeg Impact and Protocol Response
USR lost its dollar peg as the influx of synthetic supply overwhelmed secondary markets dropping to fractions of a dollar in several liquidity pools. Resolv Labs quickly confirmed the exploit stating that while 50 million unbacked USR were minted the underlying collateral pool remains fully intact and no reserve assets were lost. The team has since paused all protocol functions to halt further malicious activity. Tracking data shows the attacker residual holdings include 11.4K ETH valued near 24 million dollars and 20M wstUSR still worth approximately 1.3 million dollars confirming that the bulk of the stolen funds had cleared before the freeze.
Recovery Efforts and Future Outlook
In the aftermath of the breach Resolv Labs has prioritized containment and incident assessment. The team has reportedly burned a portion of the attacker controlled USR tokens and is investigating potential signer compromises. While no concrete compensation framework is finalized the protocol is preparing a redemption plan for users who held positions before the exploit potentially starting with allowlisted addresses. Resolv has advised all users to avoid interacting with related assets on secondary markets until the audit is complete and the system is secured.
This incident follows a growing trend of exploits targeting smart contract vulnerabilities and liquidity mechanisms across DeFi protocols, as seen in recent cases like the NFT liquidity platform attack where digital assets were drained through similar on-chain weaknesses.









