Access control vulnerabilities are far more than mere technical glitches; they represent some of the most financially devastating attack vectors in today’s digital landscape. From decentralized blockchain protocols to massive centralized exchanges, the ability of an unauthorized actor to bypass security boundaries often results in a total system compromise. This guide serves as an operational blueprint to identify, mitigate, and eliminate these risks through a defense-in-depth approach, ensuring every entry point is fortified against increasingly sophisticated cyber threats.
The Architectural Blueprint: Building on Solid Foundations
A secure system begins with its architecture, where security is treated as a core component rather than a last-minute addition. Most high-profile breaches occur because basic security foundations were either ignored during the design phase or poorly implemented during the development cycle. By establishing a robust architectural framework, organizations can ensure that even if a single component fails, the overall system remains resilient against unauthorized intrusion.
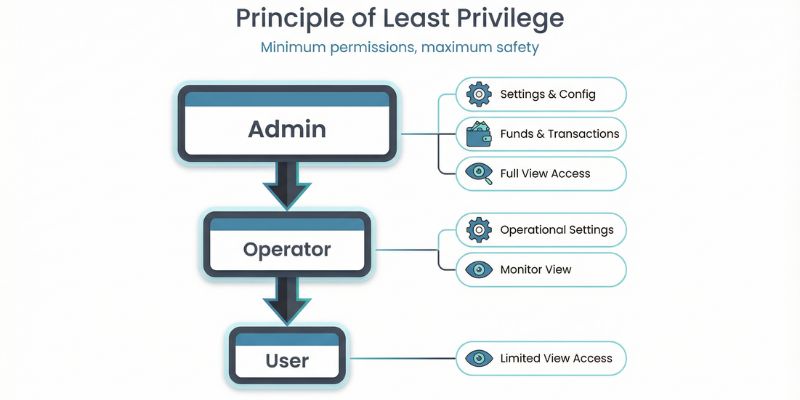
The Principle of Least Privilege (PoLP)
The most fundamental rule in security is that no user, process, or system should ever have more power than is absolutely necessary to perform its primary function. When systems grant overly broad permissions, they create an unnecessarily large attack surface where a single compromised credential can lead to a catastrophic data breach. Implementing PoLP requires a deep understanding of organizational workflows and a strict commitment to restricting access to the absolute minimum at all times.
- Role-Based Access Control (RBAC): organizations must implement strict RBAC, ensuring that permissions are mapped exclusively to specific job functions rather than to individuals.
- Time-Bounded Access: Privileges should never be permanent; implementing “Just-in-Time” access ensures that permissions expire automatically after a set period to reduce long-term risk.
- Privilege Escalation Workflows: Any sensitive action, such as moving large amounts of capital or changing system configurations, must require a multi-step approval process.
- Auditability: Every single permission change or access request must be logged with an immutable timestamp to ensure full accountability and forensic capability.
Multi-Layered Authorization (Defense in Depth)
Relying on a single security check is a recipe for disaster in high-stakes environments like finance or blockchain. Logic flaws, API vulnerabilities, or simple parameter manipulation can often allow an attacker to bypass a lone security gate. Defense in Depth involves placing multiple, independent security controls throughout the system so that an attacker is forced to break through several layers to reach the target data.
- Validation Boundaries: Authorization must be checked at every level starting from the initial API gateway, through the internal application logic, and finally at the database storage layer.
- Fail-Secure Defaults: Systems must be designed to deny access by default; if a permission check fails, times out, or is missing, the system must automatically block the action.
- Whitelist over Blacklist: Security teams should focus on only allowing “known-good” authorized entities rather than trying to maintain an impossible list of “bad” actors.
- Consistent Verification: Never assume a user is authorized just because they passed a previous check; re-verify identity and permissions for every sensitive request.
Smart Contract Security: Hardening the Decentralized Web
In the world of blockchain, “code is law,” which means a single mistake in a smart contract’s access control can lead to irreversible financial losses. Unlike traditional software, blockchain transactions cannot be undone, making the operational security of smart contracts the most critical part of any decentralized protocol. Developers must treat every state-changing function as a high-value target for hackers.
Protecting State-Changing Functions
The most common and damaging vulnerability in smart contracts is the “Missing Modifier” flaw in critical functions. If a function that transfers funds, updates price feeds, or changes contract ownership lacks an only Owner or only Authorized modifier, any user on the network can execute it. This oversight has led to some of the largest DeFi hacks in history, where attackers simply called a function that was meant to be private.
- 100% Coverage: Every single function that has the power to change the state or balance of the contract must have a verified access control modifier applied to it.
- Standardized Libraries: Developers should use battle-tested, community-audited libraries like OpenZeppelin’s AccessControl rather than attempting to write custom, unverified logic.
- Automated Audits: Tools like Slither, Mythril, and Echidna should be integrated into the CI/CD pipeline to catch missing modifiers before any code is deployed to the mainnet.
- Function Visibility: Ensure that functions are correctly marked as internal or private unless they absolutely need to be accessible to the public or external contracts.
Case Study: Arbitrum Access Control Exploit A recent incident on Arbitrum (ARB) perfectly highlights this risk. An attacker gained control by updating ProxyAdmin permissions after the project’s deployer lost access to their account. The estimated loss reached $1.5 million as the attacker seized control of the USDGambit and TLP projects, eventually bridging the stolen funds to Ethereum and laundering them through Tornado Cash.
🚨ALERT🚨Our system has detected multiple suspicious transactions on the #ARB network involving a proxy contract, resulting in an estimated loss of ~$1.5M.
Preliminary analysis suggests that the single deployer of the #USDGambit and #TLP projects may have lost access to their… pic.twitter.com/QHwxdRO0Bu
— 🚨 Cyvers Alerts 🚨 (@CyversAlerts) January 5, 2026
The Centralization Risk (Admin Keys)
Many “decentralized” protocols are actually controlled by a single admin key, creating a massive single point of failure. If this private key is stolen through phishing or malware, the attacker gains total control over the protocol’s assets. Transitioning from a single-key model to a distributed governance model is essential for long-term security.
- Multi-Signature (Multi-Sig) Wallets: Use a threshold system (like a 3-of-5 setup) for any administrative action to ensure no single person can compromise the entire system.
- Timelocks: Critical changes, such as contract upgrades, should be placed behind a 48 to 72-hour timelock to allow for community oversight and emergency intervention.
- Secure Key Storage: Admin keys should never be stored on a connected computer; Hardware Security Modules (HSMs) or air-gapped cold storage are mandatory.
- Emergency Pause Mechanism: Implement a “circuit breaker” that allows authorized guardians to pause the contract immediately if a hack is detected.
Centralized Exchange (CEX) and API Security
Centralized platforms handle massive amounts of user data and billions in assets, making them the ultimate targets for privilege escalation. Because these systems operate off-chain, they face traditional web vulnerabilities that can be used to bypass authentication and gain unauthorized access to internal management tools. Protecting the bridge between the user interface and the backend database is the most critical operational task for a CEX.
Preventing IDOR and Injection Attacks
Insecure Direct Object References (IDOR) occur when an attacker accesses another user’s private data by simply changing a number or ID in an API request. This is often combined with SQL injection, where malicious code is inserted into input fields to manipulate the database. Without strict ownership validation, these flaws allow attackers to drain thousands of user accounts simultaneously.
- Resource Ownership Checks: The system must verify that the authenticated user making the request actually owns the specific resource, such as a wallet address or transaction history.
- Parameterized Queries: To prevent SQL injection, developers must use prepared statements and parameterized queries for every single database interaction.
- UUIDs over Integers: Using non-guessable Universally Unique Identifiers (UUIDs) makes it nearly impossible for attackers to guess or iterate through record IDs.
- Input Sanitization: All user-provided data must be strictly validated and sanitized on the server side before it is ever processed or stored.
Session and Credential Management
Weak session management and predictable tokens often lead to session hijacking. It is vital that session tokens are generated securely, stored safely, and that their entire lifecycle is managed to prevent attackers from impersonating legitimate users.
- Secure Token Generation: Use cryptographically secure random number generators to create tokens with at least 256 bits of entropy.
- Cookie Security: Use the HttpOnly flag to prevent JavaScript from stealing tokens and the Secure flag to ensure they are only transmitted over encrypted HTTPS connections.
- Absolute Timeouts: Enforce strict session limits, such as 8 hours for standard users and 1 hour for administrators, to prevent sessions from staying open indefinitely.
- Password Hashing: Passwords must be stored using modern, adaptive hash functions like Argon2id or bcrypt, combined with a unique salt for every user.
- Account Lockout: Implement progressive lockout policies that trigger after a set number of failed authentication attempts to thwart brute-force attacks.
Case Study: Step Finance Treasury Exploit The critical need for endpoint security was proven by the Step Finance exploit, where $40 million was stolen from its treasury due to the compromise of an executive’s personal device. This incident highlights how a single weak link in a supply chain can lead to massive losses. Such events are frequently detailed in the latest crypto hacks Database 2025, emphasizing the urgent need for executive-level device hardening.
Audit, Monitoring, and Incident Response
Without comprehensive monitoring and audit logs, detecting an ongoing attack is nearly impossible. Organizations must maintain continuous operational discipline and a real-time alerting system to identify and stop threats as they happen.

- Immutable Audit Logs: Store all audit logs in append-only storage or use blockchain anchoring to ensure they cannot be altered or deleted by an intruder.
- Real-Time Alerting: Set up immediate alerts for failed authentications, unauthorized privilege escalation attempts, or unusual patterns in resource access.
- Containment Procedures: If a breach is detected, the team must be able to instantly suspend affected accounts and revoke all active session tokens.
- Forensic Analysis: After an incident, reconstruct the attacker’s entry point and path to identify the root cause and prevent future occurrences.
- Third-Party Management: Vendors and external partners must be restricted to separate authentication pools with time-bounded access.
Conclusion
Access control is not a one-time setup; it is a continuous operational discipline. According to the most recent findings in the crypto hacks report 2025, access control failures remain a leading cause of asset loss in the industry. By committing to rigorous security engineering, comprehensive testing, and constant vigilance, organizations can significantly reduce their risk exposure. Technical controls are only half the battle clear policies and regular independent audits are what ultimately ensure long-term resilience in an ever-evolving threat landscape.