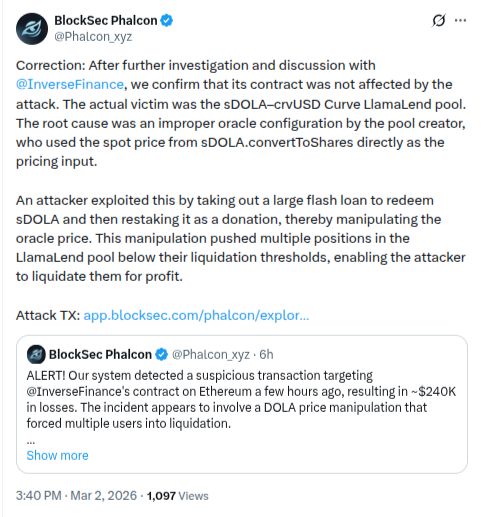
A decentralized finance (DeFi) incident that initially raised concerns about a potential exploit at Inverse Finance has now been clarified, with security researchers confirming that the protocol’s core contracts were not compromised. Blockchain security firm BlockSec issued a correction after conducting further investigation and discussions with the Inverse Finance team. According to the firm, the actual issue occurred within the sDOLA–crvUSD Curve LlamaLend pool, rather than Inverse Finance itself.
Attack Details
-
Targeted Protocol: DOLA / DolaSavings
-
Blockchain: Ethereum (ETH)
-
Estimated Loss: ~$240,000
-
Transaction Hash:
0xb93506af8f1a39f6a31e2d34f5f6a262c2799fef6e338640f42ab8737ed3d8a4
Oracle Configuration Identified as Root Cause
The investigation determined that the exploit stemmed from an improper oracle configuration implemented by the pool creator. Specifically, the pool relied directly on the spot price from sDOLA.convertToShares as its pricing input.
Security experts explained that using a spot price in this manner can introduce manipulation risks, as it may be temporarily influenced by large transactions. This vulnerability opened the door for price distortion within the lending pool.
Flash Loan Used to Trigger Liquidations
According to the analysis, the attacker executed the exploit using a large flash loan. The borrowed funds were used to redeem sDOLA tokens and then restake them as a donation, effectively manipulating the pool’s price mechanism.
This artificial price shift caused multiple borrower positions in the LlamaLend pool to fall below their liquidation thresholds. The attacker subsequently liquidated these positions, generating an estimated profit of approximately $240,000.
No Impact on Core Protocol
BlockSec emphasized that Inverse Finance’s smart contracts were not directly affected by the exploit. The vulnerability was isolated to the specific pool’s oracle setup rather than the core protocol infrastructure.
The incident highlights ongoing risks in DeFi ecosystems, particularly when integrating pricing mechanisms and oracle feeds. Experts note that even when primary protocol contracts remain secure, misconfigurations at the pool or integration level can still expose users to significant risk.