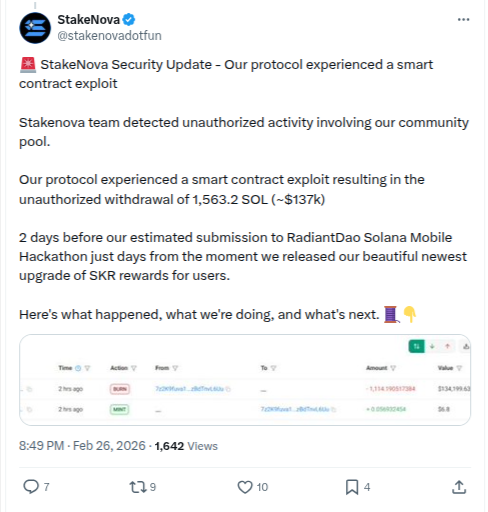
The Solana-based staking protocol StakeNova has confirmed a smart contract exploit that resulted in the unauthorized withdrawal of 1,563.2 SOL, valued at approximately $137,000. The incident, disclosed through the project’s official statement, comes just days before the team’s planned submission to the RadiantDao Solana Mobile Hackathon and shortly after a recent upgrade to its SKR rewards system.
According to StakeNova’s official security update, unusual activity was detected in the protocol’s community pool, prompting an internal investigation. The developers soon confirmed that an attacker had exploited a vulnerability in the smart contract, allowing them to drain funds without authorization. The team has since paused affected systems, begun forensic analysis, and is working with security experts to determine the root cause of the exploit.
Exploit Details and Timeline
StakeNova stated that the exploit occurred shortly after they released a new upgrade to their SKR rewards mechanism. While the update aimed to improve user incentives and platform efficiency, it appears the changes may have introduced or exposed a vulnerability that was later exploited. The breach was detected quickly, but not before the attacker successfully withdrew funds from the community pool.
Blockchain evidence shows the movement of funds in the transaction where 1,563.2 SOL was drained, confirming the unauthorized withdrawal described by the team.
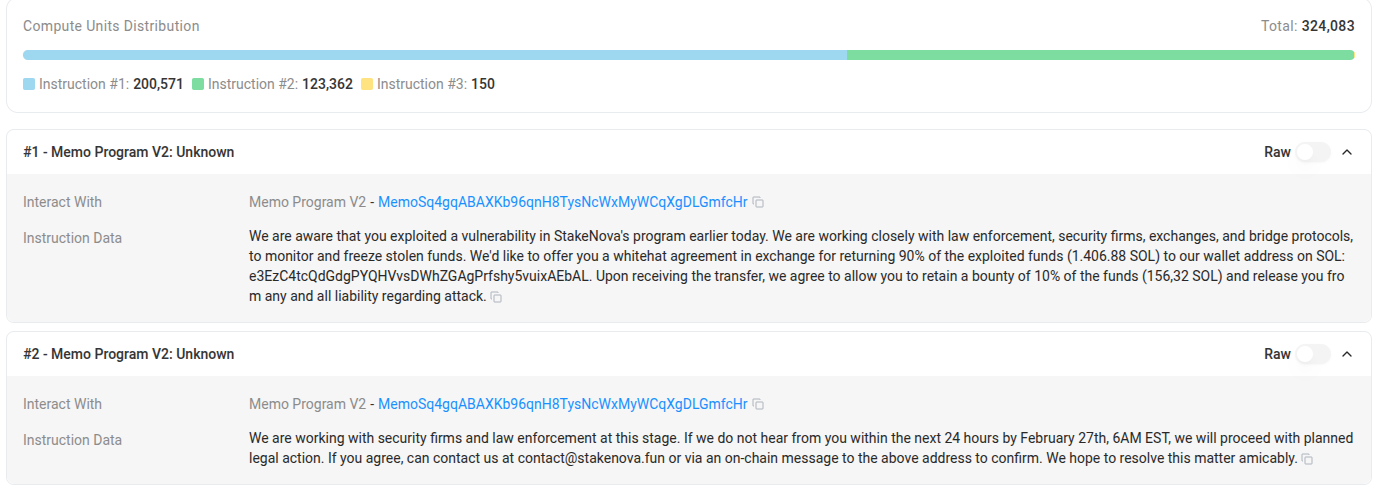
White Hat Offer to Attacker
In an attempt to recover the stolen assets, StakeNova publicly addressed the exploiter with a white hat proposal. The team offered the attacker the option to return 90% of the funds, equivalent to 1,406.88 SOL, while keeping 10% – 156.32 SOL – as a bounty. In exchange, StakeNova pledged to release the exploiter from liability and not pursue legal action.
The proposal was delivered directly through an on‑chain message sent to the attacker’s wallet, giving a 24‑hour deadline to respond before further legal and investigative action would begin.
Impact on Users and Protocol
StakeNova has assured users that the exploit was limited to the community pool and that they are evaluating ways to compensate affected users. The team has also stated that no private keys were compromised, and the attack was confined to the vulnerable contract logic.
The incident has nonetheless raised concerns about the risks associated with rapid feature deployment in DeFi ecosystems. StakeNova’s exploit occurred shortly before a major hackathon submission, highlighting how tight development timelines can sometimes leave insufficient time for comprehensive security audits and testing.
Security Response and Next Steps
StakeNova says it is conducting a full post‑mortem analysis and plans to implement additional safeguards before relaunching affected features. The team intends to introduce automated audit tools, external security reviews, and stricter code deployment procedures to prevent similar incidents.
The project also pledged to provide transparent updates to its community as the investigation continues. Depending on the attacker’s response to the white hat offer, the outcome could range from full recovery to permanent loss of funds.
Broader Implications for DeFi
Smart contract exploits continue to be a persistent challenge across the decentralized finance landscape. A recent incident involving a price-oracle misconfiguration that led to a major fund drain from a lending protocol demonstrated how external data feed dependencies can become attack vectors when validation checks are missing.
Even relatively small-scale attacks can damage user trust and highlight the importance of rigorous security practices. Experts often stress the need for continuous monitoring, automated auditing tools, and staged feature rollouts to minimize risk. In another notable case, a smart contract configuration flaw that resulted in more than $1 million in losses showed how even small deployment mistakes or incorrect parameters can quickly escalate into major financial incidents.
For StakeNova, the coming weeks will be critical. The team must not only address the vulnerability and recover funds if possible but also rebuild confidence among users and partners. Transparent communication and strong remediation efforts will likely determine whether the protocol can recover from the incident.