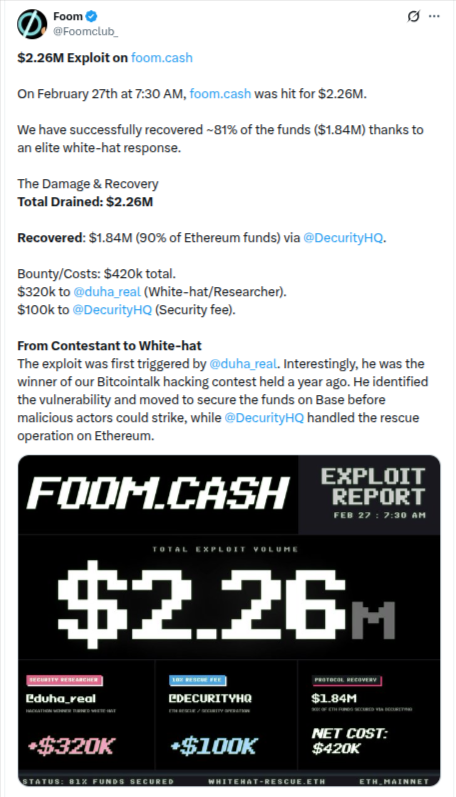
In a significant security breach, the decentralized finance platform Foom.cash was exploited for approximately $2.26 million on February 27th. However, thanks to the swift intervention of elite white-hat hackers and security researchers, the platform has successfully recovered $1.84 million (81%) of the stolen funds.
The Vulnerability: How the Exploit Happened
The breach was not a simple password theft but a sophisticated technical exploit targeting the platform’s Smart Contract layer.
-
The Flaw: The root cause was identified as a deployment error within the Groth16 verifier, a critical component used for Zero-Knowledge Proofs (ZKP) to validate transactions.
-
Forged Proofs: Due to this smart contract misconfiguration, the system became vulnerable to “Forged Proofs.” This allowed the attackers to submit invalid data that the contract mistakenly verified as legitimate.
-
The Drain: By tricking the smart contract into believing these forged proofs were valid, the exploiters authorized unauthorized withdrawals across both the Ethereum and Base blockchains. A detailed Proof of Concept (PoC) has since been shared, outlining how the vulnerability was technically executed.
The Role of @duha_real
One of the most remarkable aspects of this recovery is the involvement of the security researcher known as @duha_real.
A year ago, Foom.cash hosted a hacking contest on Bitcointalk, which @duha_real won. When the live exploit began on February 27th at 7:30 AM, he identified the vulnerability in real-time. To prevent malicious actors from draining the remaining assets, he moved quickly to secure the funds on the Base network before they could be stolen.
Simultaneously, the security firm DecurityHQ managed the rescue operation on the Ethereum mainnet, securing 90% of the ETH-based funds.
Recovery Costs and Bounties
Foom.cash has prioritized transparency and rewarded those who protected the protocol. The total cost of the recovery and security fees amounted to $420,000:
-
$320,000 Bounty: Awarded to @duha_real for his critical role in securing the funds on Base.
-
$100,000 Fee: Paid to @DecurityHQ for their professional security and rescue operations.
Current Status
With $1.84 million now secured, the team is working to finalize the recovery of the remaining 19% of the funds. The deployment error has been patched, and the protocol is undergoing further audits to ensure long-term safety for its users.

















