The Resolv Labs protocol was exploited for approximately $25 million on March 22, 2026. The attacker used only 200,000 USDC as initial capital to mint 80 million $USR tokens by exploiting a flaw in the completeSwap() function. The minted tokens were staked as wstUSR, swapped for stablecoins, and finally converted to ETH. The $USR token price dropped ~80% following the attack.
| Item | Value |
| Initial Capital Used | 200,000 USDC |
| USR Minted (illicit) | 80,000,000 USR |
| ETH held post-exploit | 11,400 ETH (~$24M) |
| wstUSR remaining | 20,000,000 wstUSR (~$1.3M) |
| $USR price drop | 80% |
Key Addresses & Transactions
| Label | Value |
| Transaction Hash 1 | 0xfe37f25efd67d0a4da4afe48509b258df48757b97810b28ce4c649658dc33743 |
| Transaction Hash 2 | 0x41b6b9376d174165cbd54ba576c8f6675ff966f17609a7b80d27d8652db1f18f |
| Attacker Wallet | 0x15CAd41e6BdCaDc7121ce65080489C92CF6de398 |
| Exploit Contract (USR Counter) | 0xa27a69Ae180e202fDe5D38189a3F24Fe24E55861 |
| USDC Contract | 0xa0b86991c6218b36c1d19d4a2e9eb0ce3606eb48 |
| USDC Recipient Address | 0xacb7027f271b03b502d65feba617a0d817d62b8e |
Step by Step Attack Flow
Deposit 100,000 USDC into USR Counter (Both Transactions)
In both transactions, the attacker deposited 100,000 USDC (approximately 99,990.20 USD) into the Resolv USR Counter contract. This initiated a swap request with the following state changes:
- swapRequests[30].state changed from 0 (PENDING) to 1 (CREATED)
- collectedFee changed from 0 to 50,000,000,000,000,000,000 (5×10¹⁹)
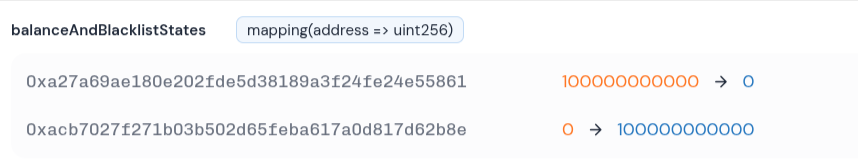
- USDC balance of USR Counter (0xa27a69…55861) changed from 100,000,000,000 to 0
- USDC balance of 0xacb7027…62b8e changed from 0 to 100,000,000,000
Call completeSwap with Inflated Target Amount
The attacker called completeSwap with a manipulated target amount value far exceeding the actual collateral deposited. The contract did not validate the amount against real collateral. It only checked that the output was greater than or equal to the minimum expected amount.
- Transaction 1 inflated amount resulted in 50,000,000 USR minted
- Transaction 2 inflated amount resulted in 30,000,000 USR minted
- Both mints came from the Null address (0x000…000) with zero real collateral backing
- A boolean flag was flipped from false to true to bypass a validation guard
Transfer of 49,950,000 USR to Exploiter (Transaction 1)
From the 50,000,000 USR minted in Transaction 1:
- 49,950,000 USR (approximately 13,967,518.50 USD) was transferred to the exploiter wallet
- 50,000 USR was retained by the contract as a protocol fee
Net gain from Transaction 1 was 49,950,000 USR for only 100,000 USDC input, which is approximately 499 times amplification
Transfer of 29,970,000 USR to Exploiter (Transaction 2)
From the 30,000,000 USR minted in Transaction 2:
- 29,970,000 USR (approximately 8,380,511.10 USD) was transferred to the exploiter wallet
- 30,000 USR was retained by the contract as a protocol fee
Net gain from Transaction 2 was 29,970,000 USR for only 100,000 USDC input, which is approximately 299 times amplification
Combined total was approximately 79,920,000 USR stolen using only 200,000 USDC, resulting in about 125 times capital amplification
Stake USR into wstUSR for Liquidity Bypass
Direct USR liquidity on decentralized exchanges was very low, making a large direct swap impractical due to extreme price impact. The attacker converted all stolen USR into wstUSR (wrapped staked USR) to:
- Access deeper liquidity pools available for wstUSR pairs
- Avoid the thin liquidity of raw USR on chain
- Reduce slippage and preserve more value
Swap wstUSR into Stablecoins and then into ETH
The attacker used decentralized exchange aggregators to convert wstUSR into stablecoins and then into ETH:
- Final holdings were 11,400 ETH (approximately 24 million USD) and 20,000,000 wstUSR (approximately 1.3 million USD)
- The large selling pressure caused the USR token to lose its peg by around 80 percent
- Most of the position was exited before the price fully collapsed
- In the USDC contract at address 0xa0b86991c6218b36c1d19d4a2e9eb0ce3606eb48, the Resolv USR Counter balance dropped from 100000000000 to 0, showing a full drain.
- At the same time, the attacker address 0xacb7027f271b03b502d65feba617a0d817d62b8e increased from 0 to 100000000000.
- This confirms that 100000 USDC was transferred out of the contract to the attacker.
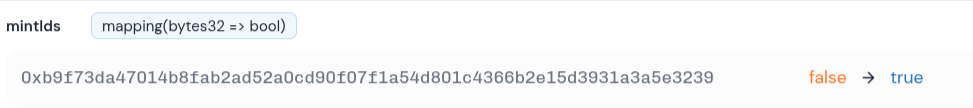
- The storage slot 0xb9f73da47014b8fab2ad52a0cd90f07f1a54d801c4366b2e15d3931a3a5e3239 changed from false to true.
- This indicates that a critical guard flag inside the contract was modified.
- As a result, the attacker was able to bypass an important validation check.
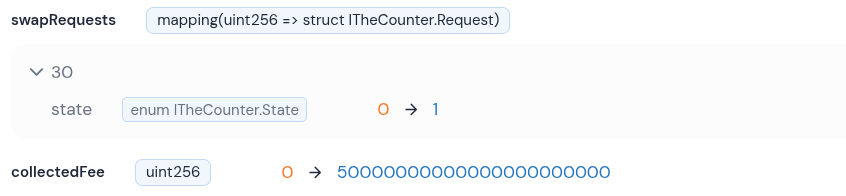
- In the TheCounter contract, swapRequests 30 state changed from 0 to 1, moving from pending to created.
- This allowed the completeSwap function to be executed on that request.
- The collectedFee also increased from 0 to 50000000000000000000 due to the inflated target amount.
Fund Flow Both Transactions
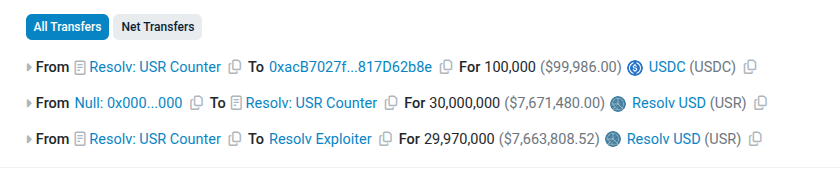
In the first transaction, the attacker transferred 100000 USDC worth approximately 99990.20 USD from the Resolv USR Counter to the recipient address 0xacB7027f…817D62b8e, effectively routing the deposit out. Following this, 50000000 USR tokens worth about 13981500 USD were minted from the null address to the USR Counter without any real collateral backing. Out of this, 49950000 USR worth approximately 13967518.50 USD was transferred to the exploiter, while a small portion was retained as a protocol fee.
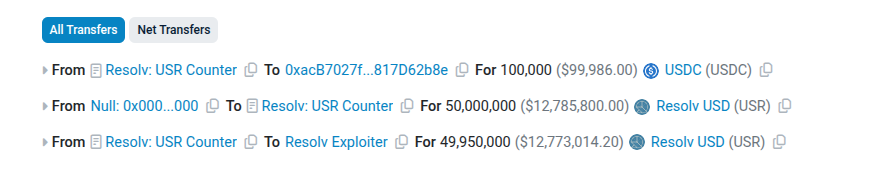
In the second transaction, the attacker repeated the process by routing another 100000 USDC worth approximately 99990.20 USD from the USR Counter to the same recipient address. Then, 30000000 USR tokens worth about 8388900 USD were minted from the null address without collateral. From this amount, 29970000 USR worth approximately 8380511.10 USD was transferred to the exploiter, with a small portion again kept as a fee.
Across both transactions, the attacker used a total of 200000 USDC to mint 80000000 USR tokens from the null address without collateral. Out of this, 79920000 USR reached the exploiter, with a total estimated value of approximately 22.35 million USD. These assets were later swapped, resulting in a final exit of 11400 ETH valued at around 24 million USD.
Vulnerability Root Cause
The completeSwap() function accepts a caller-supplied _targetAmount but never verifies it against actual collateral deposited. It only checks that the output exceeds the user’s minimum expectation, not whether the mint amount is legitimate.
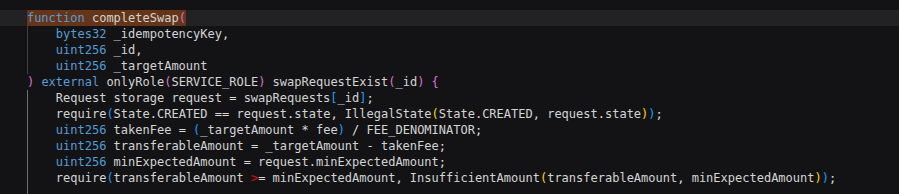
Record the actual collateral amount on-chain per swap ID at deposit time. Cap _targetAmount to that recorded value and reject anything higher.









