January 2026 proved to be a costly month for the cryptocurrency ecosystem, with security incidents affecting individual users, decentralized finance protocols, exchanges, and infrastructure projects. Over the course of the month, 25 security-related incidents were publicly reported, ranging from phishing attacks and smart contract exploits to access-control failures and account compromises.
Of these 25 incidents, 19 resulted in confirmed on-chain financial losses, while the remaining six involved compromised accounts or disclosed vulnerabilities without quantified monetary impact. Based strictly on verifiable loss data, the total confirmed financial damage for January 2026 reached $350,745,400.
What made the month particularly notable was not the number of incidents, but how heavily losses were concentrated. One event alone, a social-engineering attack targeting an individual wallet holder, accounted for more than four-fifths of the total value lost.
How the Losses Were Calculated
The $350.7 million figure reflects only incidents where a clear dollar value was disclosed or could be verified through on-chain data. Account takeovers, social-media compromises, and security alerts without asset extraction were included in the incident count but excluded from loss totals to avoid inflating the numbers.
In total:
- 25 incidents were reported
- 19 involved confirmed financial loss
- 6 involved no quantified loss
This distinction is important, particularly for financial reporting, where separating operational risk from realized losses helps present a more accurate picture of ecosystem impact.
Where the Money Was Lost
Across the 19 monetized incidents, losses varied widely in size. Most incidents resulted in losses below $5 million, and many were well under $1 million. However, one extreme outlier significantly altered the overall picture.
Confirmed Financial Losses by Incident
| Incident | Funds Lost (USD) |
| Social Engineering Victim | 282,000,000 |
| Truebit | 26,500,000 |
| SwapNet | 16,800,000 |
| SagaEVM | 7,000,000 |
| Makina (Makinafi) | 4,130,000 |
| Aperture Finance | 3,670,000 |
| Yo Yield | 3,700,000 |
| TMX | 1,400,000 |
| Arbitrum (USDGambit/TLP) | 1,500,000 |
| XPlayer (XPL) | 717,000 |
| IPOR USDC Fusion Optimizer | 336,000 |
| Polycule (PMX) | 230,000 |
| Holdstation | 192,000 |
| SynapLogic | 186,000 |
| PGNLZ token | 100,000 |
| HypurrFi | 84,000 |
| FutureSwap | 74,000 |
| OLY token holders | 63,400 |
| Valinity | 63,000 |
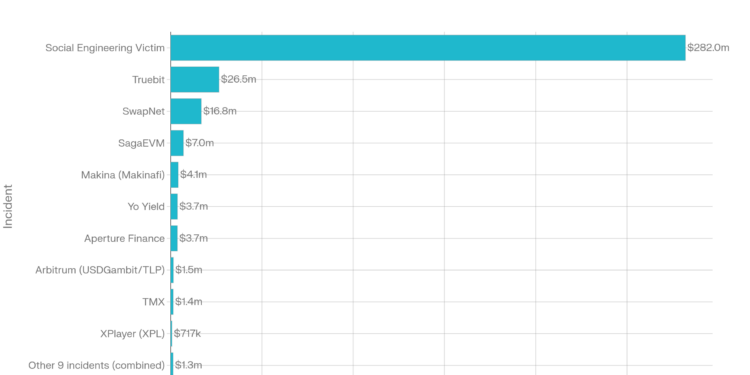
Taken together, these figures show how uneven January’s losses were. The single largest incident alone represented roughly 80.4% of the total monthly loss, while the remaining 18 incidents combined accounted for less than $70 million.
The $282 Million Social-Engineering Incident
The most damaging event occurred on January 10, 2026, when an individual lost $282 million worth of Bitcoin and Litecoin after falling victim to a phishing and social-engineering attack. The incident did not involve a protocol exploit, smart-contract bug, or infrastructure failure. Instead, the attacker manipulated the victim into disclosing wallet recovery information, enabling direct asset transfers.
Because of its scale, this incident dominated January’s loss statistics. It also underscored how individual custody failures particularly when large balances are involved can have a greater financial impact than multiple protocol-level exploits combined.
#PeckShieldAlert ZachXBT reported that on January 10, 2026, a victim lost $282M+ worth of $LTC & $BTC due to a hardware wallet social engineering #scam.
The attacker has bridged 928.7 $BTC (~$71M) to #Ethereum (19,631.1 $ETH), Ripple (3.15M $XRP), and Litecoin (77.2K $LTC) via… pic.twitter.com/6uJ3pdmdnS
— PeckShieldAlert (@PeckShieldAlert) January 19, 2026
Smart Contract Exploits Remain Persistent
While social engineering drove the largest loss, smart-contract vulnerabilities continued to account for a substantial portion of non-phishing damage during the month. The most significant of these was the Truebit exploit, where an integer overflow vulnerability allowed attackers to mint tokens at no cost and sell them on the open market, resulting in $26.5 million in losses.
Other notable contract-related incidents included SwapNet, Aperture Finance, TMX, and Polycule, affecting multiple blockchains such as Ethereum, Base, Arbitrum, BSC, and Polygon. These incidents highlighted recurring issues around arithmetic safety, approval handling, and insufficient validation logic.
Cross-Chain and Infrastructure-Level Incidents
January also saw losses linked to cross-chain activity. The SagaEVM incident, which resulted in $7 million in losses, involved coordinated malicious contract deployments followed by asset transfers to Ethereum. While serious in financial terms, the incident did not involve validator compromise or consensus failure and was limited to specific components of the network.
Oracle and Execution Design Failures
Not all losses were the result of direct exploits. Several incidents stemmed from weaknesses in oracle design or execution safeguards. Makina (Makinafi) lost $4.13 million after a flash-loan-based oracle manipulation, while Yo Yield suffered a $3.7 million loss due to extreme slippage during a vault operation.
These events demonstrated how economic assumptions and execution parameters can expose protocols to significant losses even when contracts operate as coded.
Flash Loan Attacks on Token Mechanics
Two smaller but technically sophisticated attacks targeted token mechanics using flash loans. XPlayer (XPL) and the PGNLZ token together lost just over $800,000, after attackers manipulated burn and liquidity mechanisms to extract value without deploying their own capital.
Access Control and Operational Security Issues
Access-control failures and operational security mistakes contributed to additional losses across multiple projects, including Arbitrum (USDGambit/TLP), IPOR USDC Fusion Optimizer, Holdstation, and SynapLogic. Combined, these incidents resulted in a little over $2 million in losses, typically due to compromised admin privileges or flawed permission checks.
Incidents Without Confirmed Financial Loss
Six incidents reported during the month including Solar, Scroll, Mithril, Darren Lau, Bitlight Labs, and HitBTC involved account compromises or vulnerability disclosures but did not include confirmed asset losses. These events were excluded from the loss total but remain relevant for understanding operational and reputational risk.
How Attacks Were Carried Out
Attack Vectors and Associated Losses
| Attack Vector | Incidents | Approx. Loss (USD) |
| Social engineering / phishing | 1 | 282,000,000 |
| Smart-contract vulnerabilities | 6 | ~53,000,000 |
| Flash-loan attacks | 3 | ~5,000,000 |
| Oracle / logic flaws | 3 | ~7,900,000 |
| Access control failures | 4 | ~2,200,000 |
| Other / unknown | 2 | ~100,000 |
Although social-engineering incidents were rare, they produced the largest financial impact. By contrast, smart-contract exploits occurred more frequently but resulted in smaller individual losses.
Recovery Remains Limited
Recovery outcomes remained minimal. Approximately $2.7 million was recovered during January 2026, representing less than 1% of total confirmed losses. Most recoveries occurred through MEV interception, white-hat intervention, or treasury-funded reimbursement. Assets moved through cross-chain bridges or privacy tools showed little chance of recovery.
What January 2026 Revealed
January’s incidents showed that loss severity, rather than incident count, now defines monthly crypto security outcomes. While protocol exploits, oracle issues, and access-control failures continue to occur, a single high-value social-engineering attack was enough to dominate the entire month’s statistics.
Similar patterns of loss concentration and recurring attack vectors have been observed in the crypto hack report 2025, which analyzes exploit trends, attack types, and recovery outcomes across a full market cycle.
As long as large balances remain under individual custody and recovery mechanisms depend on user behavior, similar loss patterns are likely to recur even if smart-contract security continues to improve.









