On April 27, 2026, ZetaChain suffered a security exploit targeting its GatewayEVM smart contract, a critical component that serves as the main entry point for all cross-chain interactions on the network. According to the official announcement, attackers exploited a vulnerability in the contract’s call function, which lacked proper access control and input validation. This allowed the attacker to forge cross-chain messages and drain funds specifically from internal ZetaChain team-controlled wallets across multiple chains, including Ethereum, Arbitrum, Base, BNB Smart Chain, Polygon, and Avalanche. Independent analytics platforms like DeFiLlama reported that the total loss amounted to approximately $300,000, roughly equivalent to 139 ETH. Importantly, the project has repeatedly confirmed that no user funds were affected, only the team’s internal wallets were impacted. Upon detecting the suspicious activity, the ZetaChain team quickly blocked the attack vector, preventing further losses, and temporarily paused all cross-chain transactions as a precautionary measure while a full investigation is underway. A detailed post-mortem report is expected soon.
There was an attack against the ZetaChain GatewayEVM contract today that impacted the internal ZetaChain team wallets only. We’ve already blocked the attack vector so no more funds can be compromised and will be releasing a detailed post mortem after we have completed our…
— ZetaChain 🟩 (@ZetaChain) April 27, 2026
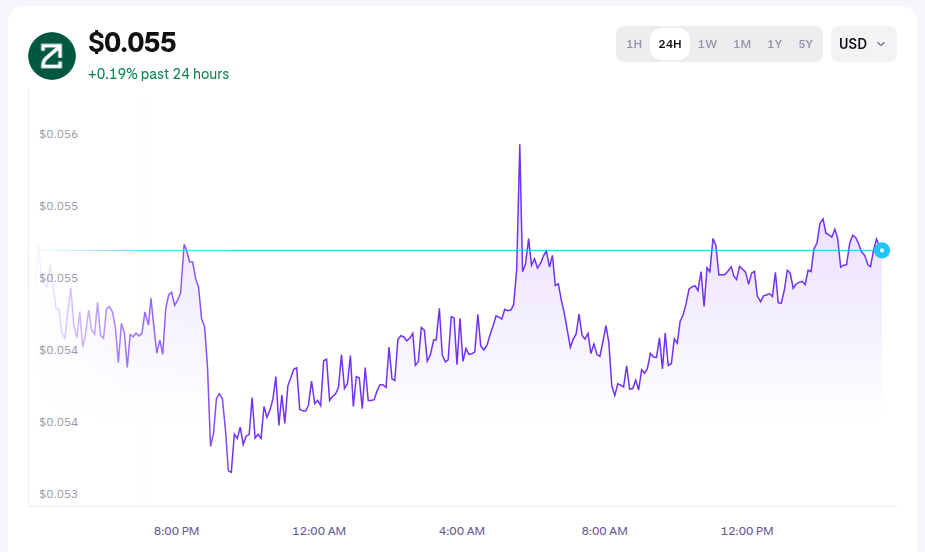
Market Reaction After the Hack
The market reacted with measured caution. ZetaChain’s native token ZETA dropped around 4.8% to 5.3% within 24 hours, trading near $0.054 with a market capitalization of approximately $73 to $77 million. The 24-hour trading range remained between $0.053 and $0.059. Despite the dip, some buying interest emerged, with over $5.36 million worth of ZETA purchased on Kraken during the decline, indicating selective accumulation at lower levels. However, overall sentiment shifted to risk-off. This exploit adds to a string of cross-chain incidents in April 2026, a month that has already seen total crypto hack losses exceed $600 million. Liquidity in ZetaChain-related pools experienced mild outflows, and the pause in cross-chain functionality is likely to limit short-term ecosystem activity, potentially keeping pressure on the token price until normal operations resume.
What Exactly Went Wrong Technically
The GatewayEVM contract is designed to handle cross-chain message passing and asset transfers between EVM-compatible chains and ZetaChain’s Universal EVM. Security researchers, including preliminary analysis from SlowMist, pointed to the absence of proper checks in the call function as the root cause. This weakness allowed attackers to impersonate legitimate cross-chain events and execute unauthorized withdrawals from team wallets. ZetaChain responded quickly by freezing the vulnerable pathway and pausing cross-chain services across the network.
Current Status and Safety Advice
- Cross-chain transactions are currently paused
- Regular on-chain activity continues normally on ZetaChain mainnet
- Users are strongly advised to revoke all approvals given to the GatewayEVM contract on Ethereum, Arbitrum, Base, and other EVM chains
- Tools like Revoke.cash can be used for this purpose
- Security firms such as Blockaid have also issued similar warnings
ZetaChain’s Vision and Future Outlook
ZetaChain is a Cosmos SDK-based Layer-1 blockchain with full EVM compatibility, aiming to provide true chain abstraction through omnichain smart contracts and native support for Bitcoin. The project has also been expanding into AI-integrated applications. While this incident represents a setback, the team’s transparent communication and swift containment have been viewed positively by parts of the community.
The upcoming post-mortem will be critical. If it clearly explains the root cause and outlines concrete security improvements, it could help restore confidence in the protocol. In the broader 2026 crypto landscape, this event serves as another reminder that interoperability solutions, while powerful, come with concentrated risks at gateway and messaging layers. Thorough audits, robust access controls, and continuous monitoring remain essential.