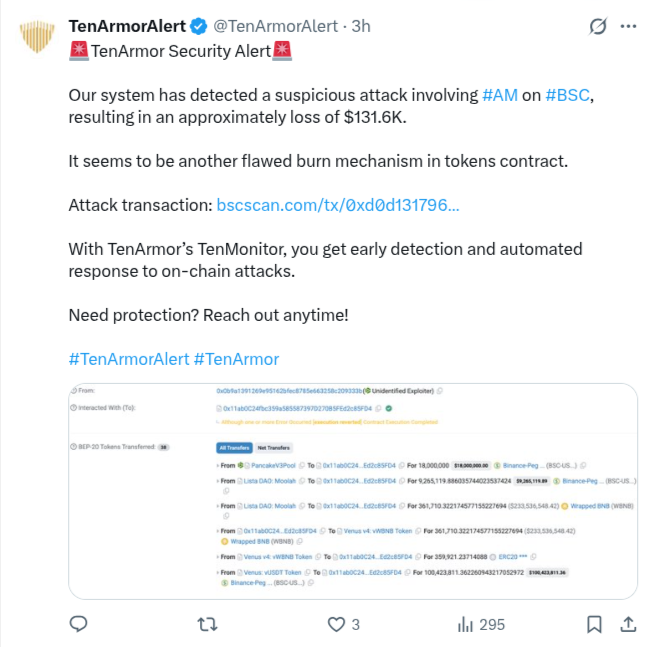
AM Token Exploit: Flawed Burn Mechanism Drains ~$131,600
Key transaction details:
- Transaction Hash: 0xd0d13179645985eae599c029574e866d79b286fbea395b66504f87f31629f859
- Timestamp: March 12, 2026, 12:40:15 AM UTC
- Attacker Wallet: 0x0B9a1391269e95162bfeC8785E663258C209333B
- Target Contract: 0x11ab0C24fbc359a585587397D270B5FEd2c85FD4
- Method Called: 0x07adecd7 (custom exploit function)
- Profit Realized: Approximately 131,572.53 BUSD (~$131,600 at the time), transferred directly to the attacker wallet
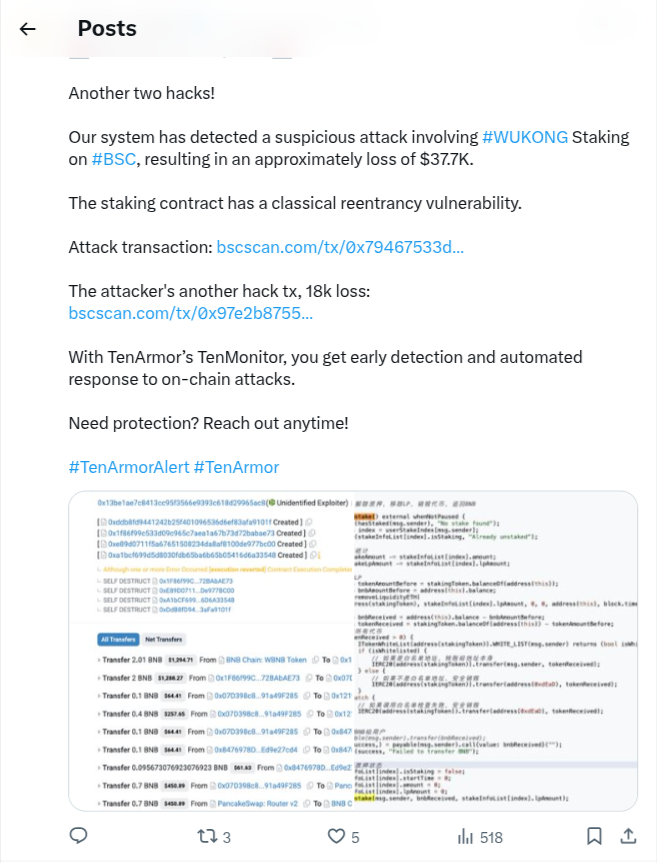
WUKONG Staking Exploits – ~$55,700 Loss in Two Attacks
TenArmor described the subsequent incidents as “another two hacks” on the #WUKONG staking contract, explicitly attributing them to a “classical reentrancy vulnerability.” This allowed the attacker to repeatedly call withdrawal functions before state updates, draining funds multiple times.Combined losses:
- First attack: ~$37,700
- Second attack: ~$18,000 (noted as “the attacker’s another hack tx”)
Attacker Wallet (from analysis of related flows): 0x13b1ae7c8413cc9f53356e69393c61bd29965ac8
Vulnerability Details: The staking contract’s unstake or claim function transferred tokens/BNB before updating user balances, total staked amounts, or emitting events. No reentrancy guard was present.The attacker deployed temporary malicious contracts (e.g., addresses starting with 0xddb8…, 0x1f86…, 0xe89d…, etc.) that interacted with the staking contract, self-destructed after draining, and routed funds back via PancakeSwap Router V2. Internal transfers included:
- 2.01 BNB (~$1,294)
- 2 BNB (~$1,288)
- Smaller amounts like 0.1 BNB and 0.4 BNB
These were converted and consolidated, with final outflows in BNB or wrapped forms.
- Primary attack: 0x79467533d4d1f332df846dc78c16fe319cd1d3a1a0f01545b4cdd7a2d3a71d22 (~$37.7K)
- Follow-up attack: 0x97e2b875552e4e82d058a775c7dd14198d15df869260235dbaf6577e5e3b13cc (~$18K)
Both occurred shortly after the AM exploit, around early March 12 UTC.
Separate Attacks, Common Chain Risks
The exploits involved different wallets (0x0B9a… for AM vs. 0x13b1… for WUKONG) and mechanisms (flash loan + burn flaw vs. reentrancy drain), indicating separate opportunistic actors rather than a coordinated group. However, the close timing and shared chain highlight how quickly vulnerabilities are scanned and exploited on BSC.No further on-chain recovery or project responses have been publicly confirmed yet. DeFi participants should prioritize:
- Thorough smart contract audits
- Use of established patterns like checks-effects-interactions
- Reentrancy guards (e.g., OpenZeppelin libraries)
- Real-time monitoring tools
These incidents also come amid a rise in scam tokens and honeypot schemes targeting users on BNB Smart Chain. In one recent case, a BSC Chain scam involving the 4Agent token reportedly drained nearly $100,000 from investors through a suspected honeypot setup, highlighting how malicious contracts can trap funds and prevent users from selling their tokens.