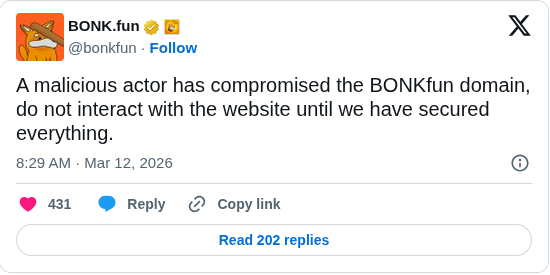
The Solana meme coin ecosystem faced a security incident after the popular launchpad BONK.fun was compromised. Hackers gained unauthorized access to a team account and injected a malicious wallet drainer into the platform’s website. The breach was confirmed by the project’s operator Tom, who warned users not to use the bonk.fun domain until the issue is resolved.
How the Hack Happened
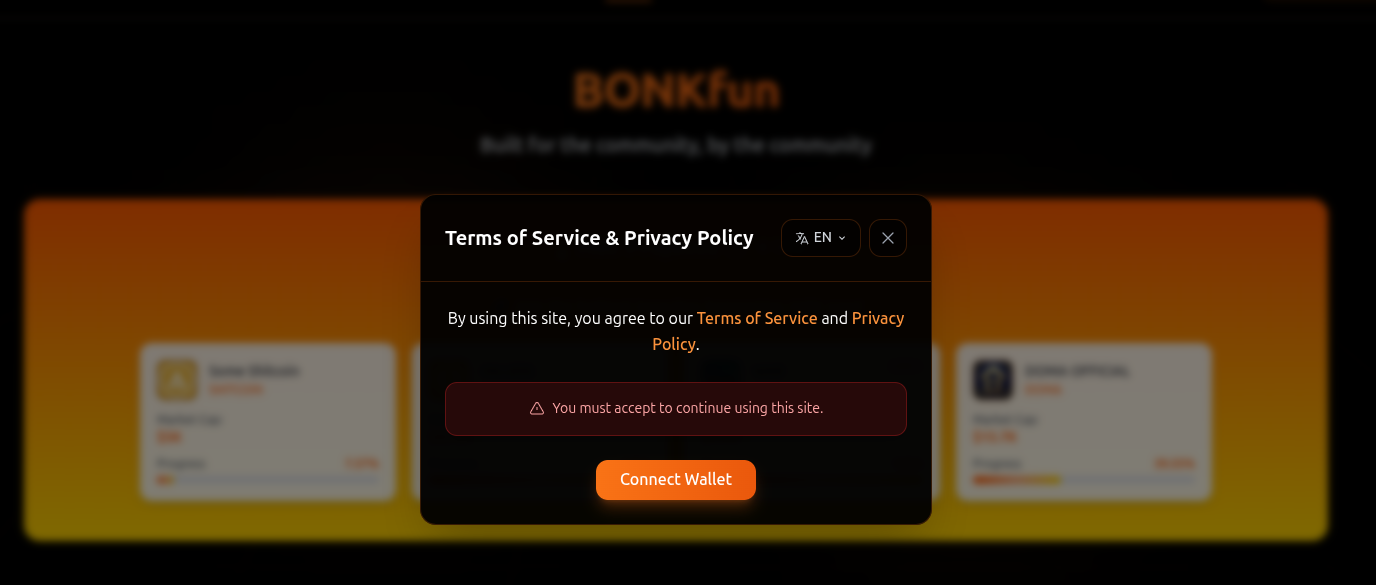
According to initial reports, attackers managed to gain control of one of the project’s internal team accounts. Using that access, they pushed a malicious update to the BONK.fun website.The injected code displayed a fake “Terms of Service” approval prompt to visitors. When users approved or signed the message, a wallet drainer script was triggered. This script requested permissions and transferred SOL and other tokens from connected wallets to attacker-controlled addresses.
Impact of the Incident
The attack did not involve a smart contract exploit on the Solana network. Instead, it was a frontend compromise caused by unauthorized admin access to the website infrastructure. The BONK.fun team stated that users who connected to the platform before the breach are not affected. Only those who visited the website after the malicious code was deployed and signed the fake prompt were at risk.
Reports indicate that some losses occurred. One user reportedly lost around $273,000, while on-chain monitoring showed at least 114 SOL drained across several wallets.
What Users Should Do
Users are advised to avoid accessing the bonk.fun website until the platform confirms that it is secure again. Those who interacted with the website recently and approved any wallet prompts should review and revoke permissions using wallet approval tools. As an additional precaution, users may move their remaining assets to a new wallet address.
Current Status
The BONK.fun team is currently working to remove the malicious code and secure the platform’s infrastructure. A full technical explanation of how the team account was compromised has not yet been released.









