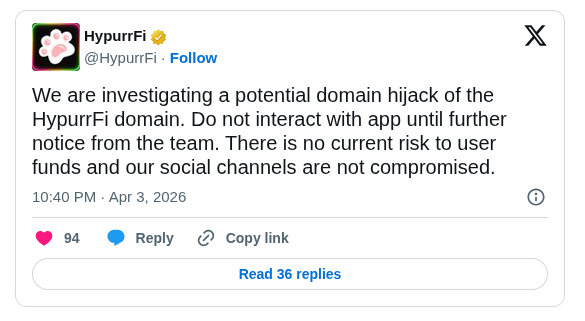
DeFi lending protocol HypurrFi has launched an urgent investigation into a suspected domain hijacking of its primary website on April 3, 2026. The team immediately advised users to avoid interacting with the app on the compromised domain until further official notice. No user funds are at risk, and the protocol’s social media channels remain fully under team control, according to the announcement. The incident highlights ongoing frontend vulnerabilities in decentralized finance platforms operating on HyperEVM, where HypurrFi maintains approximately $30 million in total value locked.
Domain Hijack Investigation Launched
On April 3 afternoon, HypurrFi detected unauthorized changes to the hypurr.fi domain, which the team attributes to a social engineering attack targeting the domain registrar. The protocol’s core infrastructure and smart contracts were not affected, allowing a swift migration of the front-end application to a secure alternative domain. Recovery efforts are underway in coordination with the registrar, identified as Openprovider, though full DNS propagation may take up to 24 hours. This marks the latest in a series of domain-related security incidents affecting DeFi projects, underscoring the need for enhanced registrar protections such as hardware key locks and DNSSEC implementation. The move to the new domain enables advanced security configurations unavailable under the .fi top-level domain.
Protocol Safeguards User Assets
HypurrFi emphasized that neither the lending protocol nor user deposits face any exposure from the incident. “There is no current risk to user funds and our social channels are not compromised,” the team stated in its initial public disclosure. The protocol has blocked the affected domain across major wallets through partnerships with security providers and continues to monitor for any residual threats. Community members have been directed to exercise caution and refrain from signing transactions linked to the old domain. This proactive response has prevented potential exploitation via malicious front-end code, preserving trust in the platform’s backend operations despite the temporary frontend disruption.
Key Incident Summary
- hypurr.fi domain reverted to attacker’s control at Openprovider registrar; team is in active communication for recovery.
- No compromise to HypurrFi smart contracts, team systems, or approximately $30 million in protocol TVL.
- Users instructed to avoid the original domain indefinitely until full resolution and DNS updates complete.