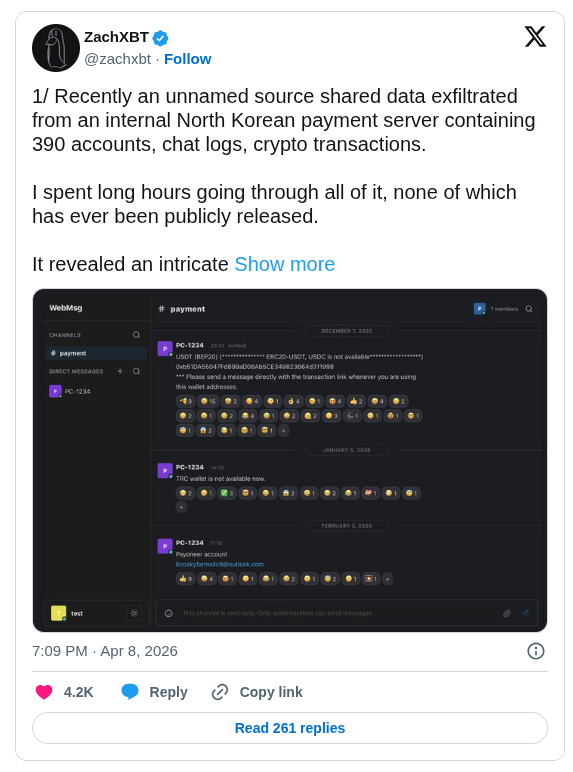
Blockchain investigator ZachXBT has released a comprehensive forensic breakdown of data stolen from an internal North Korean payment server. The dataset, obtained from a compromised DPRK IT worker’s device via an unnamed source, includes 390 user accounts, detailed chat logs, and full cryptocurrency transaction records. The operation successfully processed more than $3.5 million in crypto inflows since late November 2025, funnelling funds through fraudulent identities and layered fiat conversion channels at an average rate of roughly $1 million per month.
Luckyguys.site: DPRK’s Internal Remittance Hub
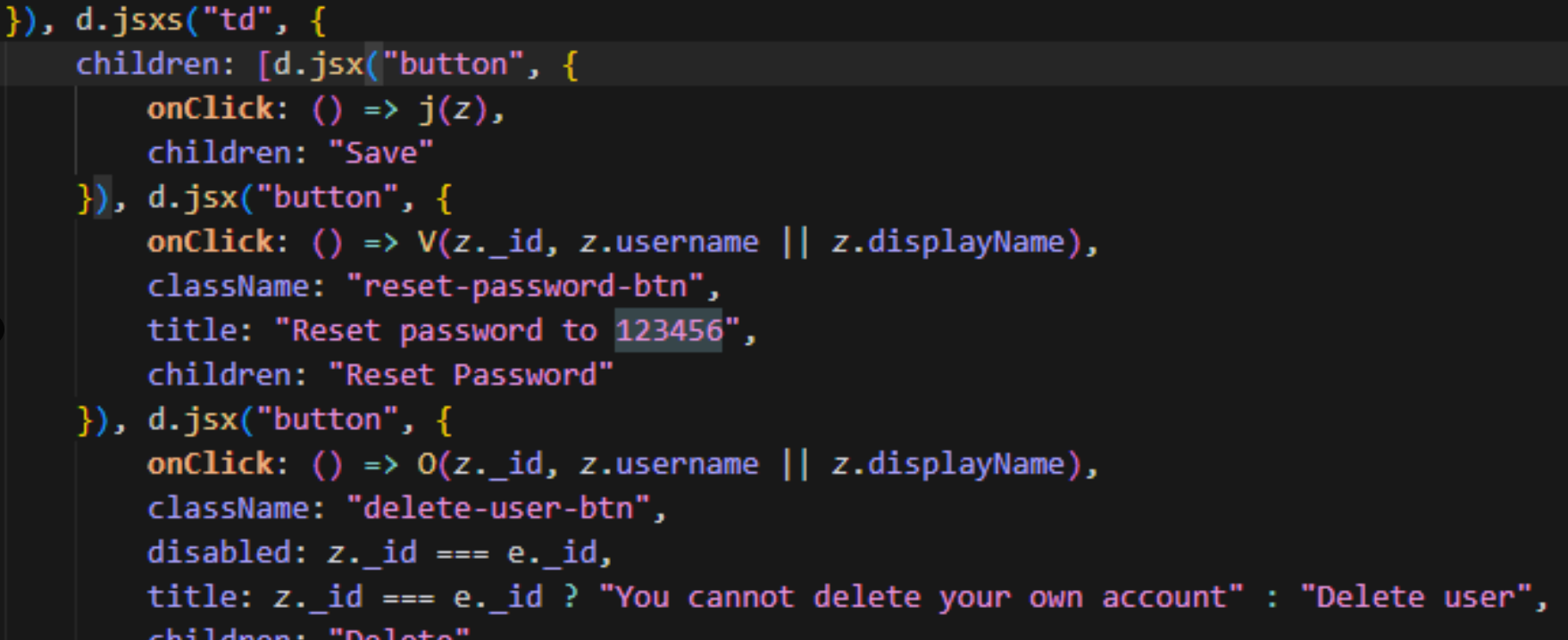
The core of the operation was luckyguys[.]site, a self-hosted messaging platform built to resemble Discord. DPRK IT workers used it exclusively to report and confirm remittances to their handlers. The server operated with the default password 123456, which remained unchanged for at least ten accounts. User profiles contained Korean names, operational cities, assigned roles, and internal group codes consistent with known DPRK overseas IT worker structures.
Three entities appearing in the records, Sobaeksu, Saenal, and Songkwang, are already designated by the U.S. Treasury’s Office of Foreign Assets Control (OFAC). All financial movements were centrally routed through the admin account PC-1234, which issued temporary login credentials for crypto exchanges and fintech platforms on a per-user basis. Direct messages between user “Rascal” and PC-1234 from December 2025 to April 2026 explicitly discuss payment confirmations and the use of Hong Kong addresses for both billing and procurement of physical goods.
Remittance Mechanics and Fiat Off-Ramps
Workers typically received cryptocurrency payments directly from client exchanges or converted earnings into fiat using Chinese bank accounts and platforms such as Payoneer. The admin account PC-1234 would then verify receipt before issuing new credentials. ZachXBT published an interactive organizational chart mapping the complete hierarchy with per-user and per-group payment totals covering December 2025 to February 2026.
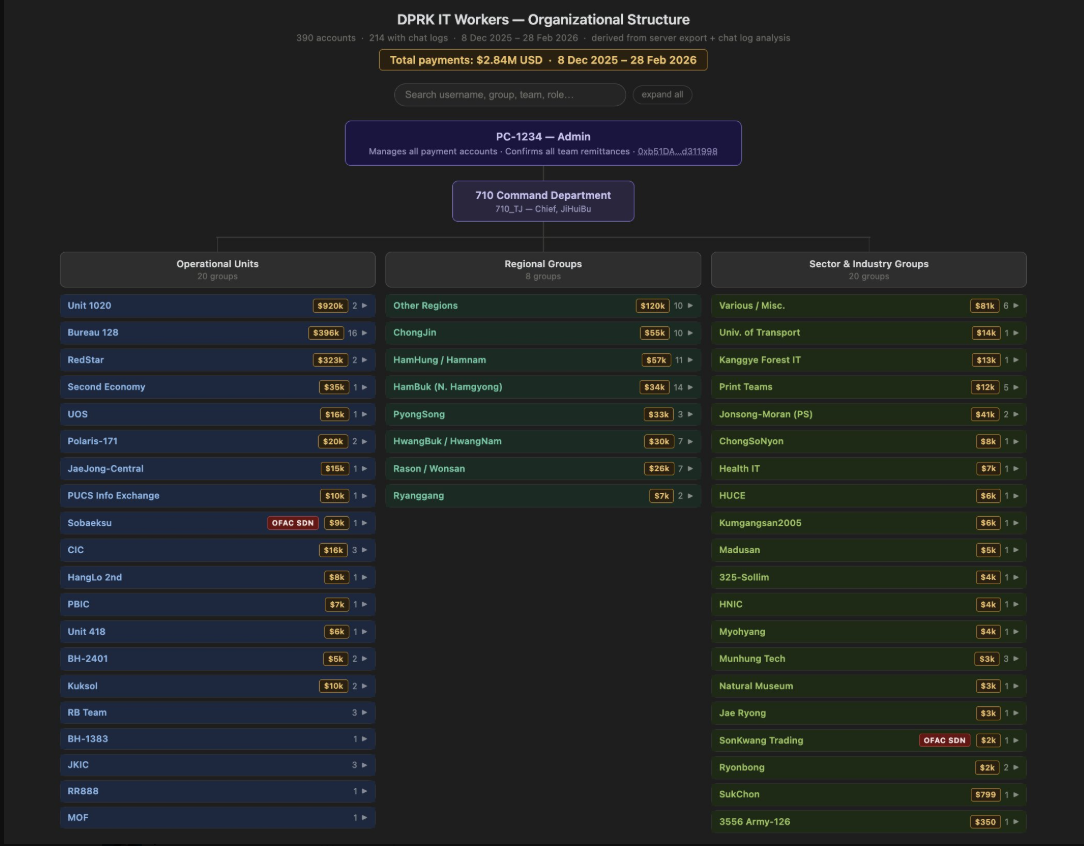
On-chain analysis connects the payment flows to previously identified DPRK IT worker clusters. The dataset also reveals systematic use of forged legal documents and multiple fabricated identities for securing remote freelance and full-time positions.
Technical Infrastructure and Operational Practices
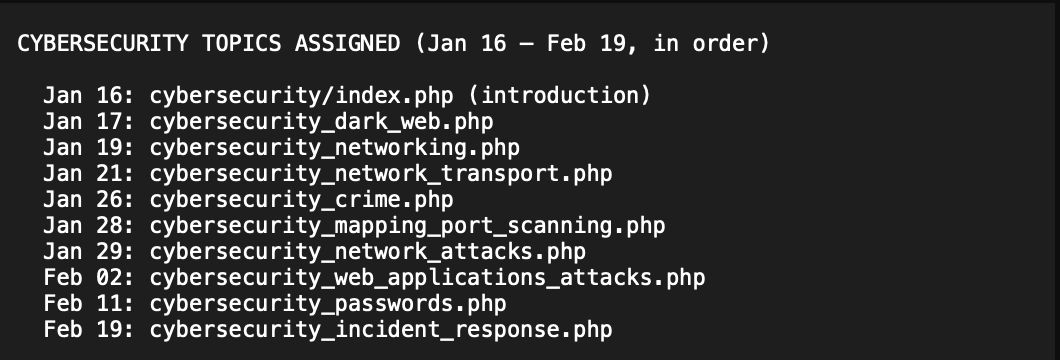
Administrators distributed 43 Hex-Rays and IDA Pro training modules between November 2025 and February 2026, focusing on disassembly, decompilation, debugging, and hostile PE unpacking techniques. Devices compromised by infostealer malware showed consistent use of Astrill VPN, IPMsg, and internal Slack channels, with one captured log indicating 33 DPRK workers operating simultaneously on the same network. Internal chats also referenced a planned theft attempt from the GalaChain game Arcano using a Nigerian proxy, along with the circulation of deepfake job-applicant blog posts to bypass recruitment screening. ZachXBT assessed the group as lower-tier compared to elite DPRK operations such as AppleJeus or TraderTraitor, noting their reliance on weak default credentials and basic operational security. The luckyguys[.]site domain was taken offline shortly after ZachXBT published his thread on April 8, although the complete dataset had already been archived.
Key Security Observations
- Default password hygiene remains dangerously weak even within state-linked financial operations.
- Payoneer and Chinese fintech services continue to function as primary fiat conversion channels for DPRK remittances.
- Infostealer infections on worker devices represent the most valuable entry point for external researchers.
- Internal server data provides significantly stronger attribution signals than on-chain analysis alone.
This leak offers rare operational visibility into the financial backbone of North Korea’s overseas IT revenue program. ZachXBT indicated he will continue expanding the public dashboard at investigation.io with additional findings from the dataset.














