March 2026 stood out as a particularly volatile and high-risk period for the global cryptocurrency ecosystem. Over the course of the month, 21 major security incidents were formally recorded, resulting in a staggering $37.6 million in confirmed on-chain losses. However, industry analysts suggest this figure represents only the visible portion of the damage, and the true economic impact is likely significantly higher. Several high-profile breaches, most notably involving LiteLLM, Bitrefill, and Neutrl, have yet to disclose their full financial losses, though their impact on user data and infrastructure integrity is confirmed.
The narrative of the month was overwhelmingly dominated by a single catastrophic event, the Resolv Labs exploit. This critical failure alone accounted for 66% of the total monthly damage, highlighting a recurring vulnerability in the DeFi space where single massive protocol failures can overshadow dozens of smaller incidents. While decentralized finance remains the primary target, the March data reveals a troubling trend where attackers are increasingly moving beyond smart contract bugs to target the human and infrastructure layers. From DNS hijacking and supply chain compromises to sophisticated phishing attacks using USDC permit signatures, the March 2026 report paints a picture of an adversary class that is rapidly outgrowing traditional security models.
Loss Metrics
- Total Confirmed Loss: $37.6M+
- Undisclosed Losses: LiteLLM, Bitrefill, Neutrl.
- Largest Single Incident: $25M (Resolv Labs).
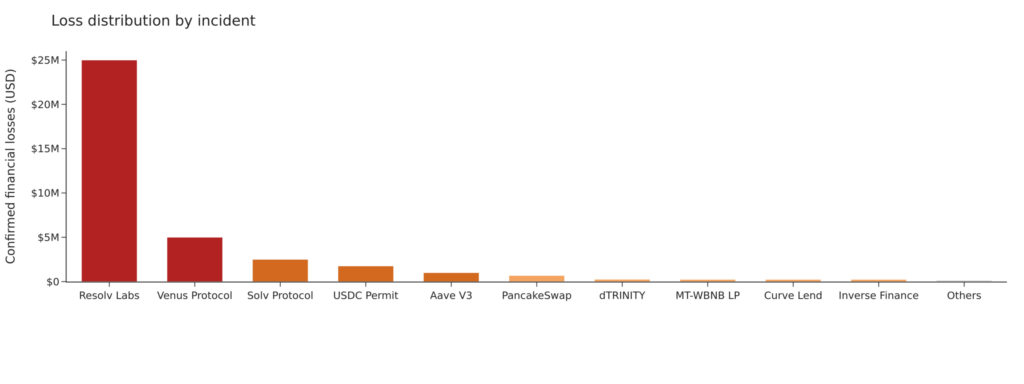
The “long-tail” distribution of security breaches reveals a stark reality in the decentralized finance landscape. While numerous small-scale incidents occur frequently, the industry’s risk profile is disproportionately defined by a few catastrophic protocol failures. A single critical event involving Resolv Labs represents a staggering two-thirds of all confirmed financial losses.
Furthermore, the top five security incidents collectively account for over 94% of the total damage recorded. This concentration of risk highlights that the most significant threats often stem from high-value targets with systemic vulnerabilities. Consequently, these massive exploits overshadow dozens of minor hacks, proving that overall market stability is heavily dependent on the security integrity of a few major platforms.
High-Severity Incidents (>$1M)
| Project | Loss | Attack Vector |
|---|---|---|
| Beanstalk Labs | $25M | Improper input validation |
| Venus Protocol | $5M | Donation attack |
| Solv Protocol | $2.5M | Protocol logic flaw |
| USDC Permit Signature | $1.76M | Phishing |
| Aave V3 | $1M | Oracle issue |
- Resolv Labs ($25M): The largest exploit of the month was triggered by an improper input validation vulnerability. The attacker bypassed security checks by injecting malicious data, allowing for unauthorized fund drainage.
- Venus Protocol ($5M): This “Donation Attack” involved the hacker sending assets to the protocol to artificially manipulate internal accounting. This skewed the collateral-to-debt ratios, allowing the attacker to withdraw excess funds.
- Solv Protocol ($2.5M): A flaw in the protocol’s core logic allowed the attacker to exploit smart contract functions in a way the developers did not intend, leading to unauthorized asset minting or transfers.
- USDC Permit Signature ($1.76M): A high-value phishing attack where a “whale” signed a malicious Permit message. This granted the attacker immediate approval to move USDC from the victim’s wallet without a direct transaction.
- Aave V3 ($1M): Even top-tier protocols are not immune. Aave V3 suffered from an Oracle discrepancy where inaccurate price feeds allowed for arbitrage-like exploitation of lending pools.
Mid-Level Incidents ($100K – $1M)
| Project | Loss | Attack Vector | Severity |
| PancakeSwap | $679K | AMM manipulation | Medium |
| dTRINITY | $257K | Deposit inflation | Medium |
| Gondi | $230K | Contract vulnerability | Medium |
| Curve Lend | $240K | Oracle issue | Medium |
| Inverse Finance | $240K | Price manipulation | Medium |
| MT-WBNB LP | $242K | Burn mechanism flaw | Medium |
| AM/USDT Pool | $131K | Flash loan attack | Medium |
- PancakeSwap ($679K): Attackers manipulated the Automated Market Maker (AMM) price curves to create an artificial price imbalance, profiting from the resulting slippage.
- dTRINITY ($257K): A “Deposit Inflation” attack where the hacker manipulated the value of shares per asset, making their small deposit appear significantly larger to the protocol.
- MT-WBNB LP ($242K): The attacker exploited a vulnerability in the token burn mechanism, which incorrectly calculated the remaining liquidity, allowing the drain of the LP pair.
- Flash Loan Attacks (Multiple): These remains a favorite for mid-tier exploits. Attackers used uncollateralized loans to provide the massive capital needed to briefly manipulate thin liquidity pools.
Low-Level & Non-Financial Incidents
- Moonwell (Governance Attack): A significant “Zero-Loss” event. Malicious actors attempted to pass a governance proposal to gain control over $1M in assets. Rapid community intervention successfully voted down the proposal.
- Steakhouse Financial (Frontend Breach): The user interface was compromised via a DNS/web-server hijack. While the smart contracts remained safe, users were at risk of connecting their wallets to a malicious “drainer” site.
- LiteLLM & Neutrl (Supply Chain): These infrastructure attacks targeted the software update pipeline and DNS settings, aiming to harvest developer credentials and user data rather than direct on-chain funds.
Attack Vector Distribution
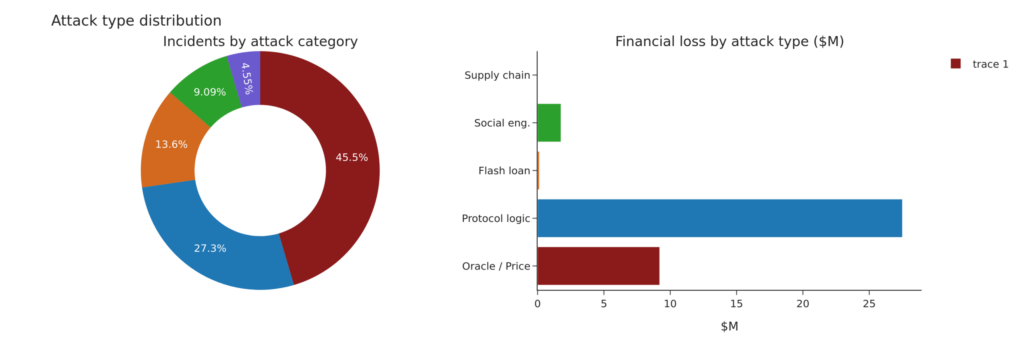
The statistical breakdown of security breaches in March 2026 reveals a significant divergence between the frequency of attacks and their actual financial impact. Oracle and price manipulation remained the most persistent threat, accounting for nearly half of all recorded incidents with 10 separate cases. However, despite being the most common method used by exploiters to drain liquidity pools and lending protocols, these attacks represented only 24.5% of the total monetary loss, amounting to approximately $9.2 million. This suggests that while oracle vulnerabilities are widespread across the DeFi ecosystem, they often result in mid-tier damages rather than catastrophic protocol collapses.
In contrast, failures in protocol logic proved to be the most devastating vector for capital flight, despite occurring less frequently. Although only 6 incidents were linked to logical flaws, they were responsible for a staggering 73.1% of the month’s total damage, totaling $27.5 million. This massive financial drain was primarily driven by the Resolv Labs exploit, confirming that a single structural error in a protocol’s core code can cause more damage than dozens of other attack types combined. Meanwhile, secondary vectors like flash loans and social engineering continued to persist but contributed a minimal fraction to the overall confirmed losses, further emphasizing that the industry’s primary systemic risk lies in complex smart contract logic.
At the same time, social engineering and phishing attacks continued to evolve. Notably, on March 31, 2026, a Kraken user allegedly lost $18.2 million in a sophisticated social engineering scam. This serves as a stark reminder that attackers are increasingly targeting human vulnerabilities alongside technical ones, reinforcing the need for stronger user awareness and defensive practices.
Personal Wallet & Transaction Safety
- Verify Before Signing: The $1.76M USDC phishing loss highlights the danger of “blind signing.” Always verify the contract address and the specific permissions (like “Permit” or “Increase Allowance”) in your wallet before clicking confirm.
- Set Custom Spending Caps: Never grant “Unlimited” token approvals. Manually set the allowance to the exact amount you need for a transaction to protect your remaining balance from future protocol exploits.
- Use Hardware Wallets: Keep the majority of your assets in cold storage. Use a separate “burner” wallet with minimal funds for interacting with new or unproven DeFi platforms.
Protocol & Infrastructure Awareness
- Beware of Frontend Hijacks: As seen in the Steakhouse Financial breach, a website can be compromised even if the code is safe. If a site looks different or asks for your seed phrase, disconnect immediately and check official social channels.
- Avoid Sponsored Search Links: Phishing sites often pay for ads to appear at the top of search results. Always use official bookmarks or trusted aggregators like DeFiLlama to access platforms like PancakeSwap or Aave.
- Diversify and Revoke: Avoid keeping all your capital in one protocol, as “Critical” failures (like Resolv Labs) can cause total losses. Regularly use tools like Revoke.cash to cancel old permissions you no longer use.
Conclusion:
The $37.6 million loss recorded in March 2026 is a conservative estimate that primarily reflects confirmed on-chain thefts. The true systemic damage to the cryptocurrency ecosystem extends far beyond these numbers, encompassing the severe erosion of user trust and the long-term impact of undisclosed infrastructure breaches. As malicious actors increasingly adopt hybrid attack strategies that combine technical code exploits with sophisticated social engineering, the industry must recognize that traditional one-time audits are no longer a sufficient defense.
The future of blockchain security must transition toward a model of continuous, real-time monitoring and proactive supply chain hardening. This involves securing every touchpoint of a protocol, including DNS settings, frontend interfaces, and third-party software dependencies. Furthermore, advanced user education is becoming a critical pillar of defense, as empowering individuals to recognize phishing attempts and malicious signature requests is often the last line of defense in preventing catastrophic financial loss. Only through this holistic approach can the ecosystem build the resilience needed to withstand an increasingly professionalized class of cybercriminals.
Reference
Download the dataset from Crypto Hack Dataset Mar 2026