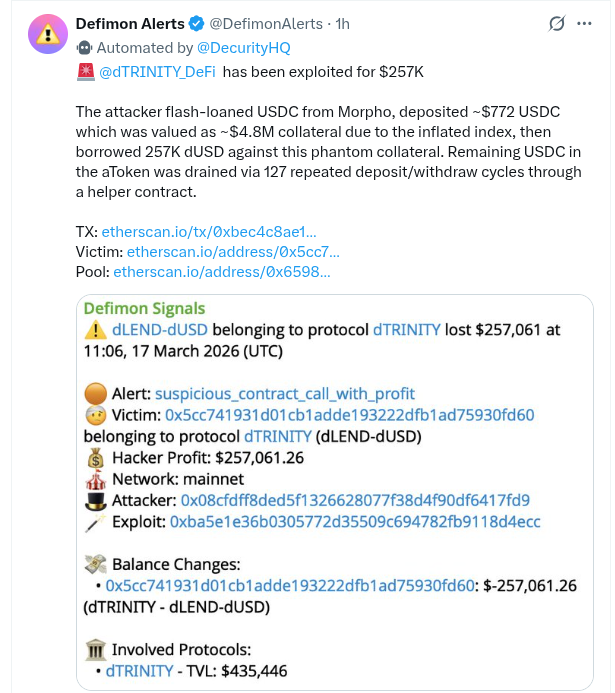
Decentralized finance (DeFi) protocol dTRINITY has confirmed a security exploit affecting the Ethereum mainnet deployment of its lending platform dLEND, resulting in losses of approximately $257,061. The protocol, which markets itself as the world’s first subsidized stablecoin system, uses revenue generated from its stablecoin to provide interest rebates for borrowers. The dTRINITY team acknowledged the incident through its official X account, stating that the protocol on Ethereum has been temporarily paused while an investigation is underway. Further updates are expected after a complete review of the attack.The exploit was first highlighted by blockchain security monitoring account DeFiMon Alerts on X, which shared early on-chain analysis and transaction details related to the suspicious activity.
How the Exploit Happened
Initial security alerts and on-chain analysis indicate that the attacker leveraged a flash loan to manipulate the protocol’s internal accounting system.
According to the analysis:
- The attacker first flash-loaned USDC from Morpho to gain temporary liquidity.
- They deposited approximately $772 worth of USDC into the dLEND-dUSD liquidity pool.
- Due to an inflated internal index or accounting error, the protocol incorrectly valued the deposit as roughly $4.8 million in collateral.
- This artificial or “phantom” collateral allowed the attacker to borrow about 257,000 dUSD from the protocol.
- Using a helper contract, the attacker then executed 127 repeated deposit and withdrawal cycles, draining the remaining USDC held within the protocol’s aToken accounting layer.
Targeted Pool and Addresses
The exploit specifically targeted the dLEND-dUSD pool, identified by the address:
- Victim Contract:0x5cc741931d01cb1adde193222dfb1ad75930fd60
The suspected attacker’s wallet address is reported as:
- Attacker Address:0x08cfdff8d8ed5f1326628077f38d4f90df6417fd9
The main exploit transaction hash has been identified as:
- Transaction Hash:0xba5e1e36b0305772d35509c694782fb9118d4ecc
Impact and Protocol Status
At the time the exploit was detected, dTRINITY’s total value locked (TVL) was approximately $435,000. Early reports suggest that no funds outside the affected pool were directly impacted, though investigations are ongoing. dTRINITY operates a subsidized stablecoin ecosystem centered around dUSD, integrated with lending through dLEND, and backed by assets from protocols such as Frax and others.
This incident appears to be separate from a smaller exploit involving dLEND reported in 2025.
Ongoing Investigation
The dTRINITY team has not yet released details about fund recovery efforts or potential compensation plans for affected users. For now, the Ethereum deployment of the protocol remains paused, and users are advised not to interact with the contracts until official updates are provided. Further information is expected as the investigation continues.
A similar issue was recently seen in another DeFi lending platform after a token crash triggered major losses within the system. In that case, theVenus Protocol exploit left about $2.15 million in bad debt following sharp market volatility.









