The first quarter of 2026 proved to be one of the most damaging periods for Web3 security in recent history. A single social engineering attack in January alone accounted for an estimated $282 million in losses, underscoring that the weakest link in the chain is increasingly human vulnerability rather than just code. Across the first three months, more than 50 distinct incidents were catalogued, ranging from sophisticated phishing campaigns and smart contract exploits to oracle manipulations and infrastructure compromises.
The data reveals a deeply fragmented threat landscape. While DeFi protocols on Ethereum continued to bear the brunt of financial losses, other ecosystems including Solana, BSC, Base, and Arbitrum faced repeated and costly breaches. Beyond direct theft, non-financial incidents such as DNS hijacks and governance account compromises surged, signaling that reputational and operational damage is expanding alongside financial harm.
Key Statistics: Q1 2026
- Total Estimated Loss: $450M+ (Combined)
- Financial Incidents: 37 (With confirmed amounts)
- Non-Financial Breaches: 15+ (Account and Infrastructure hacks)
- Largest Single Hit: $282 million (Social Engineering)
- Chains Affected: 10+ (Including Ethereum, Solana, BSC, and Base)
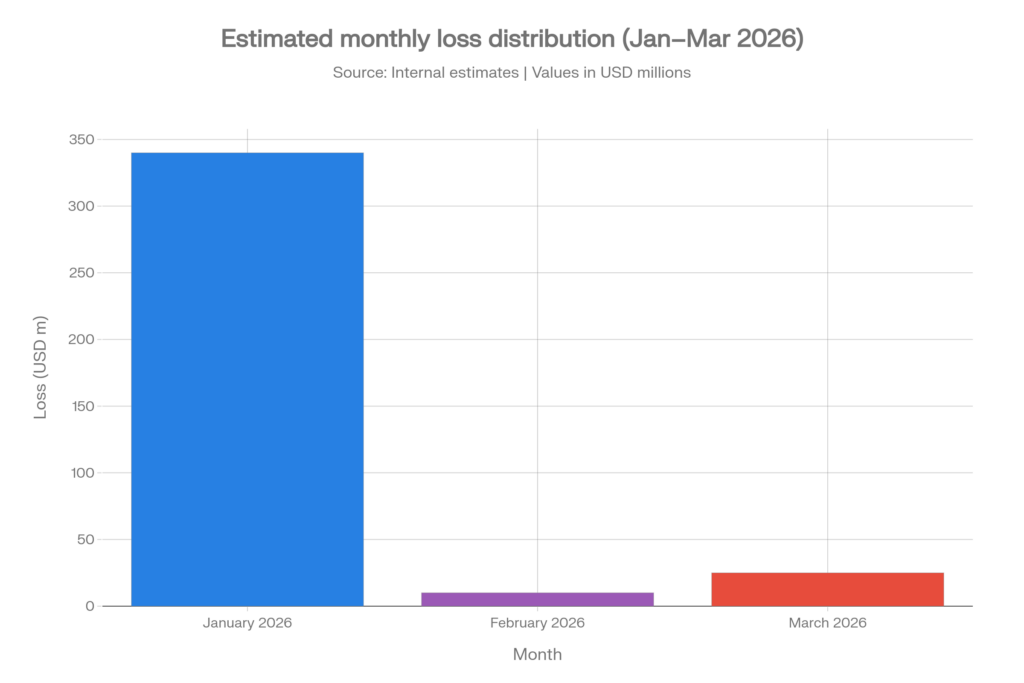
The financial data for the first quarter of 2026 reveals a highly volatile landscape, with the vast majority of losses concentrated at the beginning of the year. January was by far the most devastating month, recording a staggering $340 million in lost assets. This massive spike was primarily driven by a single high-profile social engineering attack, which alone accounted for nearly 80% of the month’s total damage. The scale of this loss set a grim tone for the quarter, highlighting how vulnerable the ecosystem remains to targeted human-centric exploits.
In contrast, the following months showed a significant cooling period, though threats remained persistent. February saw the lowest activity of the quarter with approximately $10 million in losses, representing a brief period of relative stability. However, this downward trend did not last, as March experienced a resurgence in exploit activity with losses climbing back up to roughly $25 million. This late-quarter uptick serves as a critical reminder that while massive single-event hits like the one in January are rare, the consistent baseline of smaller, sophisticated attacks continues to pose a steady threat to Web3 security.
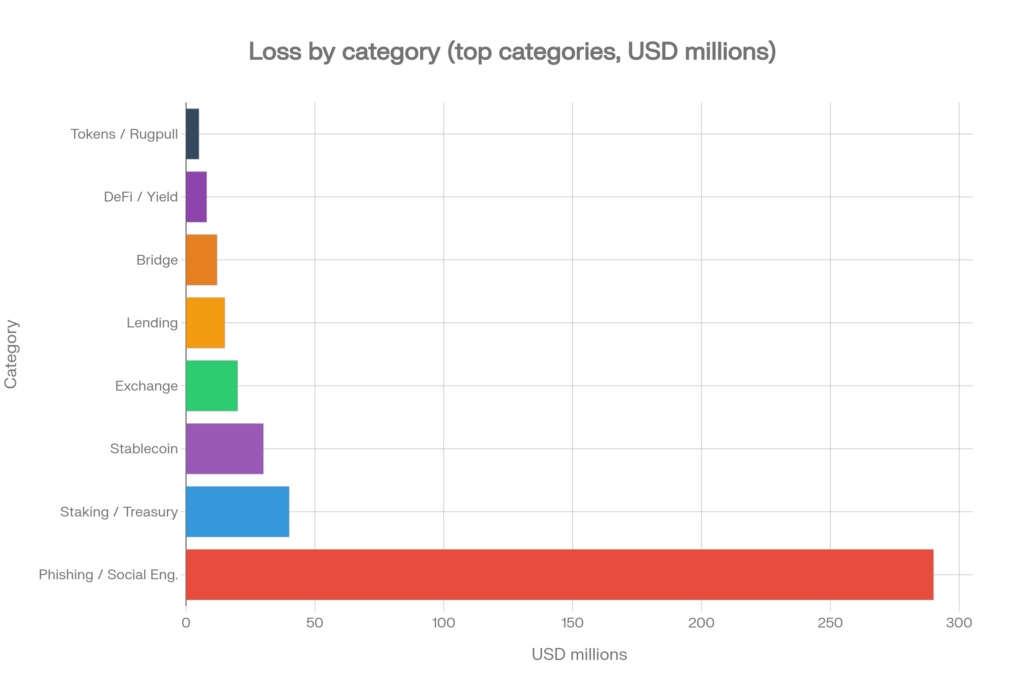
- Phishing and Social Engineering emerged as the primary threat vector, accounting for a massive $290 million in losses, which dwarfs all other categories combined this quarter.
- Staking and Treasury protocols faced the second-highest financial impact with approximately $40 million lost, highlighting significant vulnerabilities in institutional-grade asset management.
- Stablecoin and Exchange sectors were also heavily targeted, suffering roughly $30 million and $20 million in damages respectively, as attackers focused on high-liquidity entry and exit points.
- Lending and Bridge infrastructure continued to show vulnerability with combined losses exceeding $25 million, emphasizing the persistent risks associated with cross-chain and credit-based protocols.
- DeFi / Yield and Tokens / Rugpulls represented the smaller portion of total losses, together contributing roughly $15 million, suggesting a shift in attacker focus toward larger-scale social and treasury exploits.
January 2026 Hack Analysis
| Project | Amount Lost | Primary Attack Vector |
| Social Engineering Attack | $282,000,000 | Phishing / Social Engineering |
| Step Finance | $40,000,000 | Access Control / Supply Chain |
| Truebit | ~$26,000,000 | Price Manipulation |
| SwapNet | ~$17,000,000 | Contract Vulnerability |
| Saga / SagaEVM | $7,000,000 | Minting / Unknown |
| Makina / Makinafi | ~$4,000,000 – $5,000,000 | Flash Loan / Oracle Manipulation |
| Yo Yield / YO Protocol | $3,700,000 | Slippage / Unknown |
| Aperture Finance | $3,670,000 | Contract Vulnerability |
| NYC Memecoin | $3,400,000 | Rugpull |
| TMX | $1,400,000 | Contract Vulnerability |
| Gyroscope | $807,000 | Unknown |
| XPlayer | $717,000 | Flash Loan |
| PMX | $230,000 | Unknown |
| SynapLogic | $186,000 | Contract Vulnerability |
| PGNLZ Token | $100,000 | Flash Loan |
| HypurrFi | $84,000 | Unknown |
| Valinity | $63,000 | Oracle Issue |
- January 2026 was catastrophically dominated by a single $282 million social engineering attack, which stands as one of the largest phishing-based exploits in Web3 history to date.
- Even without the primary outlier, January losses exceeded $60 million, driven largely by the $40 million Step Finance exploit on Solana caused by access control and supply chain failures.
- Truebit and SwapNet suffered a combined $43 million in losses due to price manipulation and contract vulnerabilities, highlighting the high risks associated with verification protocols and multi-chain deployments.
- Newer ecosystems and low-cap tokens remained prime targets, evidenced by the $7 million Saga/SagaEVM minting exploit and the $3.4 million NYC Memecoin rugpull.
- The month’s data underscores a fragmented threat landscape where attackers successfully pivoted between sophisticated technical contract breaches and large-scale human-centric phishing campaigns.
February 2026 Hack Analysis
| Project | Amount Lost | Primary Attack Vector |
| Blend Protocol | ~$10,000,000 | Oracle Manipulation |
| IoTeX Bridge | ~$4,400,000 – $8,000,000 | Access Control / Key Leakage |
| CrossCurve | ~$3,000,000 | Contract / Input Validation |
| FOOMCASH | $2,260,000 | Contract Vulnerability |
| Moonwell | ~$1,700,000 | Oracle / Governance Attack |
| Holdstation | $192,000 – $462,000 | Access Control / Unknown |
| Ploutos Money | $388,000 | Rugpull |
| SOF Token | $248,000 | Flash Loan Attack |
| LAXO Token | $190,000 | Flash Loan Attack |
| Revert (Base) | $50,000 | Unknown |
- February was defined by two major protocol-level exploits, including Blend Protocol’s $10 million oracle manipulation on Stellar and the $4.4–8 million IoTeX bridge compromise on Ethereum.
- The IoTeX incident highlighted a devastating recurring pattern where private key leakages and access control failures in bridge infrastructure continue to threaten cross-chain liquidity.
- Governance mechanisms emerged as a direct attack surface, evidenced by the Moonwell exploit on Base which utilized a combination of oracle and governance-based attack vectors.
- Cross-chain and privacy-focused protocols faced significant pressure, with FOOMCASH losing $2.26 million and CrossCurve suffering a $3 million loss due to input validation failures.
- Small-cap tokens and smart wallet infrastructure became tactical targets, seen in the Ploutos Money rugpull and the emerging threat against Holdstation’s smart wallet security.
March 2026 Hack Analysis
| Project | Amount Lost | Attack Vector |
|---|---|---|
| Resolv Labs | $25M | Access Control / Input Validation |
| Venus Protocol | ~$2–5M | Oracle / Donation Attack |
| Solv Protocol | ~$2.5–2.7M | Logic Issue |
| Aave V3 | $1M | Oracle Issue |
| AM/USDT Pool (BSC) | $131K | Flash Loan Reserve Manip. |
| MT-WBNB LP | $242K | Burn Mechanism Manipulation |
| BCE Token | $679K | Reserve Manipulation |
| dTRINITY | $257K | Flash Loan / Inflation Attack |
| Gondi | $230K | Contract Vulnerability |
| DBXen | $150K | Logic / Access Control |
| V4 Swap Router | $42K | Access Control |
- March saw a distributed spread of incidents, headlined by the $25 million Resolv Labs stablecoin exploit on Ethereum caused by access control and input validation failures.
- Oracle-related vulnerabilities intensified across major lending protocols, with Aave V3 ($1M), Venus Protocol ($2–5M), and Resolv Labs all facing critical issues regarding price feed reliability.
- BSC remained a hotspot for sophisticated AMM manipulation, including the $242K MT-WBNB LP burn mechanism exploit and the $679K BCE Token reserve manipulation.
- Lending protocol mechanics were targeted via inflation attacks, specifically the $257K dTRINITY flash loan exploit on Ethereum which demonstrated a high level of technical understanding from attackers.
- The exploit landscape expanded into NFT finance (NFTFi), evidenced by the $230K Gondi contract vulnerability, a sector that has historically seen lower audit coverage than traditional DeFi.
Infrastructure & Account Compromises
Beyond direct financial theft, the first quarter of 2026 was marked by a persistent wave of infrastructure and account compromises that targeted the very foundations of Web3 trust. January saw a high concentration of account takeovers affecting critical ecosystem players, including Bitlight Labs, the Scroll L2 network, and influential media figures like Darren Lau. These incidents, alongside security vulnerabilities at HitBTC and the compromise of trading bots like Mithril, demonstrate that attackers are increasingly prioritizing the control of communication channels and administrative interfaces to stage future exploits or spread misinformation.
The trend shifted toward more sophisticated infrastructure attacks in February and March, with a notable rise in DNS hijacking and supply chain vulnerabilities. High-profile targets such as Arbitrum Governance, Steakhouse Financial, and Neutrl faced domain-level threats, while the PyPI attack on LiteLLM highlighted the growing risk of supply chain compromises in the developer ecosystem. Even centralized services and community platforms like Bitrefill and Solar were not immune, as social engineering continued to be a primary tool for bypassing traditional security layers, proving that reputational damage and operational disruption are now as central to the threat landscape as direct monetary loss.
Attack Vector Distribution
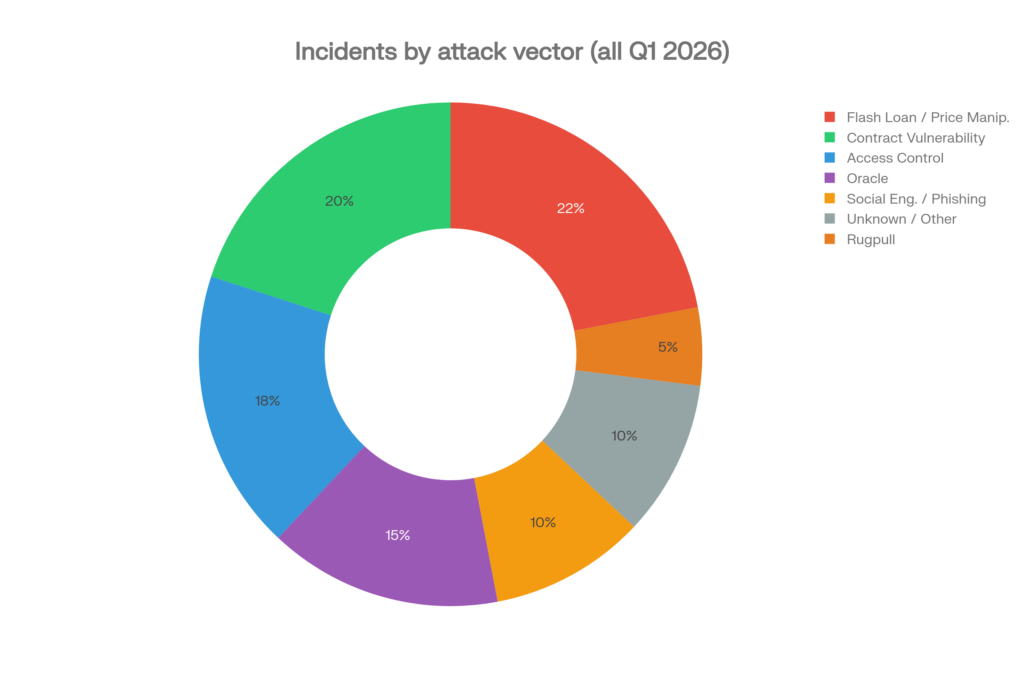
Flash Loan and Price Manipulation attacks were the most frequent category by count, appearing in at least 10 incidents. These attacks exploit the atomicity of blockchain transactions, borrowing large sums without collateral within a single block to manipulate on-chain prices or drain reserves. BSC proved particularly vulnerable, with multiple AMM pools and token contracts falling to this vector in all three months.
Access Control failures were the second most common vector and, critically, responsible for some of the quarter’s largest losses. Step Finance ($40M), IoTeX Bridge (approximately $8M), and Resolv Labs ($25M) all suffered because of inadequate controls over privileged operations. Private key compromise is categorically the hardest to recover from: once keys are lost, protocol authority is surrendered entirely.
Oracle Manipulation emerged as a defining threat to lending and stablecoin protocols. Aave V3, Venus Protocol, Moonwell, Blend Protocol, and Valinity all suffered oracle-adjacent exploits. Price feeds that rely on thin liquidity pools or poorly secured external data sources remain a systemic weakness across lending primitives.
Social Engineering and Phishing, though fewer in count, were responsible for the single largest dollar loss of the quarter ($282M). DNS hijacking, domain takeovers, and account compromise attacks against media personalities and governance participants showed that the ecosystem’s off-chain infrastructure is as exploitable as its on-chain contracts.
Rugpulls, such as NYC Memecoin and Ploutos Money, continue to demonstrate that despite greater awareness, exit scams remain profitable and routine in low-cap token markets. Smart contract audits are rarely performed on memecoin launches, and the pseudonymous nature of deployers makes accountability nearly impossible post-fact.
Conclusion
The first quarter of 2026 reinforced three persistent structural weaknesses that continue to define the Web3 security landscape. First, human vulnerability remains the primary attack vector, as the quarter’s largest single loss was driven by social engineering rather than a code exploit, while non-financial incidents like DNS hijacks and phishing campaigns far outpaced what on-chain defenses alone can address. Second, oracle infrastructure is clearly not keeping pace with DeFi complexity, with at least five significant exploits across lending protocols in just three months proving that reliance on manipulable price feeds has become a systemic risk requiring standardized, resistant design. Third, the inconsistent application of access control discipline across various chains remains an operational failure, as privileged functions were repeatedly exploited despite the availability of well-understood mitigations like multi-signature requirements and time-locks. Ultimately, the quarter signals a dangerous expansion of the threat surface where smart wallets, governance systems, and even supply chain packages have become viable targets, necessitating a shift toward treating security as a continuous practice rather than a simple pre-launch checklist.
Reference
Download the dataset from Crypto Hack Dataset Mar 2026














