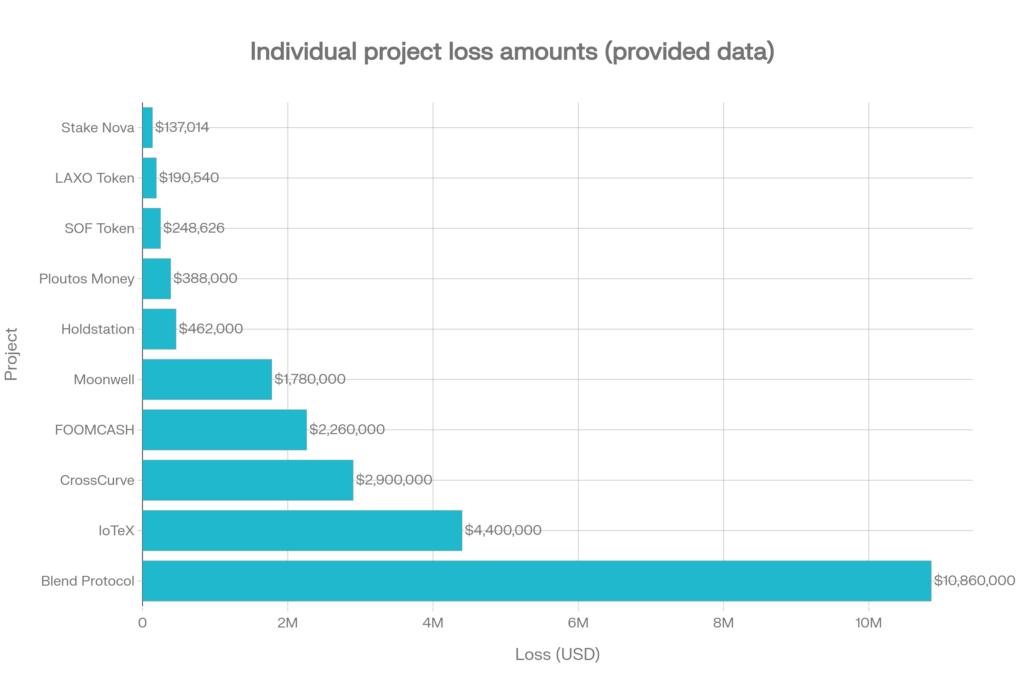
Between February 2 and February 26, 2026, the crypto ecosystem recorded at least $23.63 million in confirmed losses across 12 reported security incidents. However, broader industry trackers estimate that total losses for February 2026 reached approximately $26.5 million, indicating additional incidents or updated loss figures beyond those detailed here. The largest single exploit during the period was an oracle-related attack on Blend Protocol, which alone caused $10.86 million in losses. Bridge exploits and oracle issues together accounted for the majority of financial damage during this period. Smaller but recurring incidents included flash loan attacks, access control failures, and contract vulnerabilities. This summary reflects confirmed publicly reported losses and may not account for undisclosed or later-updated impacts.
Key risk categories observed:
- Oracle & Price Feed Issues: $12.64M combined
- Bridge Vulnerabilities: $7.3M combined
- Contract Vulnerabilities & Flash Loans: $2.69M combined
- Access Control Failures: $4.86M combined
- Rug Pulls: $388K
- Business Logic Errors: $137K
- Social Engineering & Account Hacks: Financial impact undisclosed in some cases
Bridges and borrowing protocols remain the most financially impacted sectors.
February 2 – Bridge Exploit
CrossCurve
On February 2, 2026, CrossCurve suffered a major bridge exploit that resulted in approximately $2.9 million in losses across Ethereum and another connected chain. The attack was linked to a smart contract vulnerability within the protocol’s cross-chain bridge infrastructure, likely involving flaws in message validation between networks. By exploiting this weakness, the attacker was able to process unauthorized transactions and withdraw funds. Bridge systems depend heavily on secure verification across multiple blockchains, so even a minor validation error can lead to significant financial damage. The incident once again highlights the systemic risk associated with cross-chain bridge architecture, which continues to be one of the most targeted areas in the DeFi ecosystem.
February 14 – Flash Loan Attack
SOF Token
On February 14, 2026, SOF Token was targeted in a flash loan attack on the BNB Smart Chain, resulting in losses of approximately $248,626. The attacker used a large, instant loan obtained without collateral to manipulate token prices and liquidity pool balances, allowing them to exploit weaknesses in the contract’s logic and withdraw profit. Flash loan attacks typically focus on tokens with low liquidity or poorly designed pricing mechanisms, where temporary market manipulation can produce outsized gains. This incident highlights how insecure liquidity mechanics and weak economic safeguards in token contracts can be rapidly exploited within a single transaction.
February 18 – Oracle Misconfiguration
Moonwell
On February 18, 2026, lending protocol Moonwell suffered losses of approximately $1.78 million due to an oracle misconfiguration. Attackers were able to exploit incorrect or outdated price feeds, allowing them to borrow assets far beyond the actual value of their collateral. Oracle-related issues are particularly dangerous for lending platforms because borrowing limits depend entirely on accurate price data. Even a minor configuration mistake can lead to significant financial damage, highlighting the critical need for multi-source oracle validation and continuous monitoring in DeFi borrowing protocols.
February 21 – Bridge Access Control Failure
IoTeX
On February 21, 2026, the cross-chain bridge infrastructure of IoTeX was exploited due to an access control vulnerability, resulting in approximately $4.4 million in losses on Ethereum. The attacker gained unauthorized access to restricted smart contract functions, enabling the withdrawal of funds from the bridge. Access control failures typically occur when administrative roles are poorly secured or when contract permissions are misconfigured. Because bridge systems manage large liquidity pools and operate across multiple networks, even minor permission errors can lead to significant financial damage, reinforcing the need for strict role-based access control and secure key management practices.
February 22 –oracle manipulation
Blend Protocol
On February 22, 2026, Blend Protocol suffered the largest security incident recorded during the reporting period, with losses totaling approximately $10.86 million. The exploit stemmed from an oracle-related issue that allowed attackers to manipulate price feeds and borrow assets using insufficient collateral, ultimately draining liquidity from the protocol. Lending platforms are particularly sensitive to oracle accuracy because borrowing limits depend entirely on real-time price data. When safeguards such as multi-source aggregation or circuit breakers are absent, manipulated price feeds can lead to significant financial damage. This incident underscores oracle manipulation as one of the most critical and financially impactful threats in the DeFi ecosystem.
LAXO Token
On February 22, 2026, LAXO Token was impacted by a flash loan attack on the BNB Smart Chain, resulting in losses of approximately $190,540. Similar to other recent token exploits, the attacker utilized borrowed liquidity obtained through a flash loan to manipulate the token’s market price and exploit weaknesses in the contract’s calculation logic. Many BSC-based token projects remain vulnerable to such attacks due to low liquidity pools and insufficient price protection mechanisms. The incident highlights the ongoing risk flash loans pose to tokens with weak economic safeguards and inadequate slippage controls.
February 25 – Access Control Incident
Holdstation
On February 25, 2026, Holdstation suffered losses of approximately $462,000 on Ethereum due to an access control vulnerability in its smart contracts. Attackers were able to call restricted functions that should have been limited to administrators or contract owners, enabling unauthorized fund withdrawals. Access control incidents often occur when role checks are missing or permissions are incorrectly configured. This case shows how even basic security mistakes in contract design and permission management can still lead to significant financial damage in DeFi systems.
February 26 – Three Major Incidents
FOOMCASH
On February 26, 2026, FOOMCASH suffered an exploit affecting its deployments on Base and Ethereum, resulting in losses of approximately $2.26 million. The incident was caused by a smart contract vulnerability that allowed attackers to manipulate contract logic and withdraw funds improperly. Operating across multiple chains increased the protocol’s attack surface, making security management more complex. Common smart contract issues such as reentrancy flaws, incorrect balance validations, or improper state updates often lead to similar exploits. This case highlights the importance of rigorous auditing and testing, especially for multi-chain DeFi deployments.
Stake Nova
On February 26, 2026, Stake Nova reported losses of approximately $137,014 following a business logic vulnerability in its staking system. Instead of exploiting a coding bug, the attacker abused flaws in the reward calculation or staking rules to extract funds. Business logic issues are often difficult to detect because the smart contract code may function as intended while the economic design contains weaknesses. Such vulnerabilities can pass standard security audits yet still lead to financial losses, highlighting the need for deeper economic modeling and stress testing in DeFi protocol design.
Ploutos Money
On February 26, 2026, Ploutos Money was reported as a rug pull on Ethereum, resulting in losses of approximately $388,000. In the incident, project insiders allegedly withdrew liquidity or investor funds intentionally, leaving users unable to recover their assets. Rug pulls typically occur in projects with anonymous teams, unlocked liquidity pools, or limited governance transparency. Despite increased awareness in the crypto sector, such exit scams continue to impact small-cap and newly launched projects.
Social Engineering & Account Takeover Incidents
February 3 –Arbitrum Governance
On February 3, 2026, a governance-related social media account associated with Arbitrum’s DAO operations was compromised in an account takeover incident. While no direct financial losses were disclosed, governance accounts hold significant authority within decentralized ecosystems. Attackers gaining access to such accounts could post malicious proposals, spread phishing links to community members, or attempt to manipulate protocol governance decisions.
These incidents typically occur due to phishing attacks, credential leaks, SIM swap attacks, or weak multi-factor authentication practices. Even when no funds are immediately stolen, compromised governance channels can damage user trust and create long-term ecosystem risk.
February 23 –WLFI
On February 23, 2026, WLFI reported a coordinated social engineering attack targeting its official Twitter profiles. Attackers likely impersonated trusted contacts or sent phishing messages to gain account access. Although no financial loss was disclosed, such incidents remain highly dangerous because they target human vulnerabilities rather than technical flaws.
Compromised social media accounts can be used to spread fake airdrops, malicious wallet links, or scam announcements that trick users into signing transactions. These attacks highlight the importance of strict operational security practices, hardware-based authentication, and strong internal access controls for project teams.
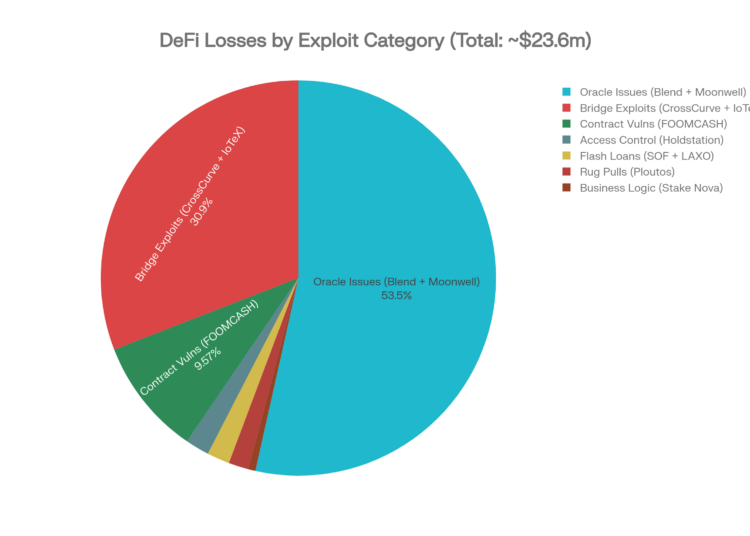
| Category | Total Loss |
|---|---|
| Oracle Issues (Blend Protocol + Moonwell) | $12,640,000 |
| Bridge Exploits (CrossCurve + IoTeX) | $7,300,000 |
| Contract Vulnerabilities (FOOMCASH) | $2,260,000 |
| Flash Loan Attacks (SOF Token + LAXO Token) | $439,166 |
| Access Control (Holdstation) | $462,000 |
| Rug Pulls (Ploutos Money) | $388,000 |
| Business Logic (Stake Nova) | $137,014 |
Oracle Risk Remains Dominant
Oracle-related vulnerabilities caused nearly half of the total losses during this reporting period. Incidents affecting Blend Protocol and Moonwell showed how manipulated or misconfigured price feeds can allow attackers to borrow more assets than allowed. Lending protocols depend heavily on accurate price data, making oracle security critical. Even small pricing errors can lead to large financial damage.
Bridges Continue to Be High-Value Targets
Bridge protocols recorded over $7.3M in combined losses from CrossCurve and IoTeX incidents. Bridges hold large pooled liquidity and rely on complex cross-chain validation systems. A single flaw in message verification or permissions can allow unauthorized withdrawals. This makes bridges one of the most attractive targets for attackers.
Access Control Failures Are Recurring
Access control weaknesses were seen again in incidents involving Holdstation and IoTeX. Missing role checks or improper admin permissions allowed attackers to call restricted contract functions. Many exploits happen not because of complex bugs, but due to basic permission misconfigurations. Strong role-based access control and secure admin key management are essential to prevent such attacks.
Flash Loan Attacks Persist on BSC
Flash loan exploits continue to impact BSC token projects like SOF Token and LAXO Token. Attackers use instant loans to manipulate token prices or liquidity pools and exploit contract logic. These attacks are common in tokens with low liquidity or weak pricing formulas. Better slippage protection and secure price mechanisms are needed to reduce this risk.
Conclusion
The February 2026 dataset clearly shows that oracle infrastructure and borrowing protocols represent the highest systemic financial risk, contributing the largest share of total losses during the period. Bridge security continues to be a structural weak point, with cross-chain validation complexity creating high-impact vulnerabilities. At the same time, repeated access control and operational security failures demonstrate that many exploits remain preventable with stronger privilege management and internal security practices. While rug pulls are still present in the ecosystem, their financial impact remains smaller compared to technically driven exploits such as oracle manipulation and smart contract flaws.
With total confirmed losses reaching $23.63 million in February, the data underscores the urgent need for stronger oracle validation safeguards, strict access control implementation, formal verification of business logic, flash loan–resistant contract architecture, and improved governance account security. This conclusion is based solely on the provided dataset and does not account for any undisclosed or unreported financial impacts.









