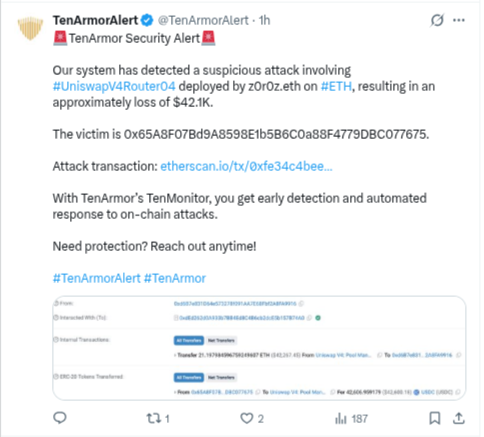
An exploit in the Uniswap V4 Router04 contract on the Ethereum network has resulted in a loss of approximately $42,100. The breach, which involved a contract deployed by z0r0z.eth, has raised immediate concerns regarding the safety of experimental routing logic in the Uniswap V4 ecosystem. According to blockchain data, a specific vulnerability within the Router04 contract allowed unauthorized access to the victim’s funds, highlighting the inherent risks associated with early-stage “Hooks” and custom routers on the mainnet.
Attack Details (On-Chain Data):
| Metric | Details |
| Victim Address | 0x65A8F07Bd9A8598E1b5B6C0a88F4779DBC077675 |
| Network | Ethereum Mainnet (ETH) |
| Assets Stolen | ~21.19 ETH and USDC stablecoins |
| Estimated Loss | $42,100 USD |
| Transaction Hash | 0xfe34c4beee447de536bbd3d613aa0e3aa7eeb63832e9453e4ef3999924ab466a |
Technical Deep Dive: How the Exploit Occurred
Security researchers believe the exploit was made possible through a flaw in how the Router04 contract handles user permissions and interactions with the Uniswap V4 Pool Manager.
-
Approval Exploitation: The victim had previously granted the Router04 contract permission (approval) to spend their tokens for swaps. In a standard scenario, the contract only moves funds as part of a legitimate user-initiated trade. However, the attacker identified a logical flaw that allowed them to “trigger” the contract into moving the victim’s funds to an external address controlled by the hacker.
-
Logical Call Flaw: Preliminary analysis suggests the router failed to properly validate the caller’s identity during specific function executions. By injecting a malicious “call,” the attacker tricked the router into thinking it was executing a valid swap, while it was actually draining the user’s wallet.
-
V4 Hook Complexity: The introduction of “Hooks” in Uniswap V4 allows for highly customizable trades, but it also increases the attack surface. In this instance, the interaction between the router’s logic and the pool’s state seems to have lacked the necessary “guardrails” to prevent unauthorized fund withdrawals.
A Crucial Lesson in “Security Hygiene”
This incident serves as a stark reminder of the dangers of “Unlimited Approvals.” In the DeFi world, most users grant contracts permission to spend an infinite amount of a specific token to simplify future trades. However, if that contract—or a router connected to it is compromised, hackers can drain every token associated with that approval.
To mitigate such risks, technical experts recommend a “Limited Approval” approach: only granting permission for the exact amount of a single transaction. Furthermore, users are urged to use tools like Revoke.cash or Etherscan’s approval checker to regularly clear out old or unnecessary permissions, ensuring that even if a contract is exploited in the future, their assets remain out of reach.
This exploit is part of a growing trend of DeFi vulnerabilities; for instance, the February 2026 crypto security report highlights that over $23 million was lost across various incidents last month alone. Staying informed about these recurring threats is the first step toward maintaining a secure on-chain presence.














